Nexus 2.0 turns your repository manager into the first line of defense against security vulnerabilities and the perfect platform to assess your exposure to open source licenses. With this release, your repository becomes more than just a place to file binary artifacts, it becomes a tool you can use to implement security policy and govern which open source licenses are used in your projects.
Nexus is in perfect position to be your OSS “sentry”: keeping watch over insecure artifacts as they are downloaded from remote repositories. Your builds and your developers request open source artifacts from Nexus all the time, and Nexus relays those requests to remote repositories downloading the open source artifacts your teams have come to depend on. While your company builds software and completes CI builds, your Nexus instance is assembling a local cache of all the artifacts used in your applications. You can scan this local proxy cache for problematic components with a feature we’ve named Repository Health Check.
Nexus 2.0: Repository Health Check
Repository Health Check connects your Nexus instance to Sonatype Insight - a service from Sonatype providing tools that let you to manage and monitor license, quality, and security data about the artifacts used in your software development lifecycle. If there’s a critical security bug in a Tomcat library used in your application, the new Repository Health Check report can tell you if this library has made it into your Nexus instance. If you are inadvertently shipping software with an AGPL dependency, Nexus can now alert you to unacceptable licensing risks.
Install Nexus 2.0 and note the new Quality column in the Nexus repository view, each repository eligible for a repository health check has a green “Analyze” button. Clicking on this button will schedule a health check with the Sonatype insight server. This green button will change to a blue button signaling that a health check is in progress.
When you submit a repository to Insight for a repository health check your data is secure. We’re not transferring any binary artifacts to the Insight service, and no identifying information about your artifacts is sent to the Insight service. The only data transmitted to Insight is a set of hashcodes for the artifacts in your repository. Once this data has been submitted, Insight then analyzes these hashcodes against a database of licensing and security vulnerability information returning a report that summarizes your exposure to security risks and various open source licenses.
Repository Health Check Summary
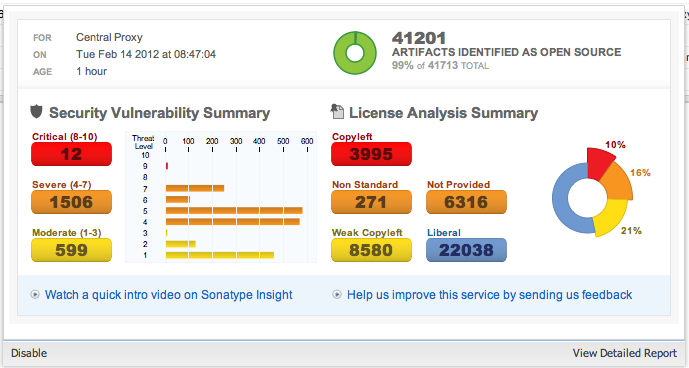
Once this analysis has been completed an analyzed repository will display top-level numbers for security and licenses issues identified in a repository. Clicking on this information will load a Summary report.
Here you see a summary report showing you high-level information about the open source artifacts identified in this repository including summary information security and licensing issues identified in a repository. You see the number of security issues identified as well as a breakdown of issues by severity: Critical, Severe, and Moderate. You will also see a breakdown of open source artifacts grouped by license type: Copyleft, Liberal, and Weak Copyleft.
Nexus Professional: Detailed Repository Health Check Reports
Nexus Professional users can drill-down into the details of this summary report to view individual security issues and license information.
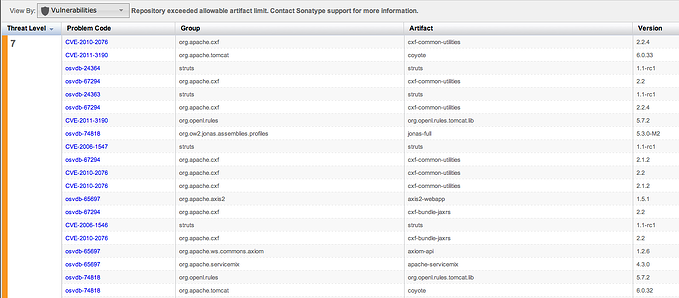
Above is a detailed security report. Insight currently tracks security vulnerabilities from the Open Soucre Vulnerability Database and the Common Vulnerabilities and Exposures lists. Each vulnerability is assigned a severity and associated with a groupId, artifactId, and version number. By scanning your own proxy repositories you can identify and address potential security vulnerabilities before they make it into production by upgrading your projects and removing the insecure dependencies.
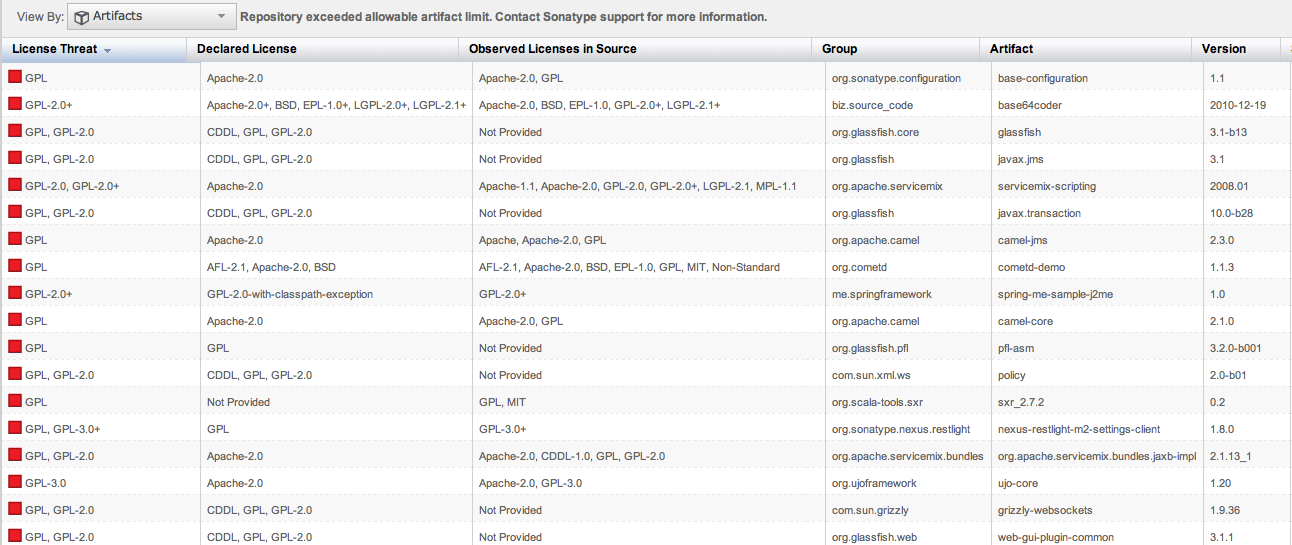
Above is a detailed licensing report. This report lists the identified license threat color coded for severity. The report also lists the declared licenses alongside a list of licenses observed from a simple scan of the project’s source code. You can use these details to assess your exposure to various open source license and start to implement policies for licenses and dependencies integrated into your software projects.
To learn more about Nexus 2.0, go to the Nexus Professional Product site to download a trial of Nexus Professional 2.0. You can also download the open source version of Nexus 2.0 by going to nexus.sonatype.org.