Over a month has passed since HeartBleed was announced to the public, and while saturation into the mainstream media likely peaked shortly after that, it can often be interesting to revisit technical revelations like this one from a layperson’s perspective.
Mind you in this case I use layperson somewhat relatively. As a member of the documentation team at Sonatype, I have exposure to some of the brightest engineering minds and thinkers I’ve ever had the pleasure to work with. Not to mention, I’m exposed intimately to the process behind the development of software using open source components.
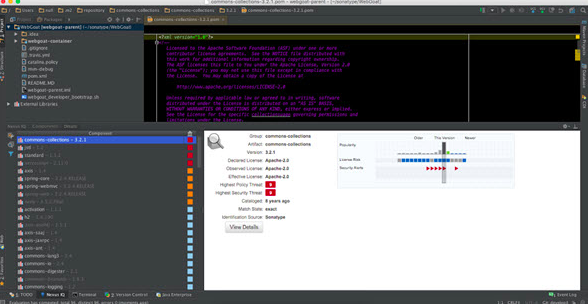
If you didn’t already know, we do a pretty good job of exposing said security risks, licensing concerns, and a number of other things (Yay Nexus!) as well. I could discuss many of the finer points around these features and/or products, though I’m certain my peers would do a far better job presenting a more technical description of things.
And therein is the trick, or really the false truth we self-deprecating (self included) “laypeople” tell ourselves
Removing the Sonatype Hat
 So, if I could beg your pardon, let me take off my Sonatype hat for just a moment and don that of a general consumer. In this wardrobe change, consider me a consumer of software applications your company produces (which I utilize) or employs (to use your service) - which in both cases it is highly likely I am. Whether it’s newfangled widgets or spacely sprockets, is not important.
So, if I could beg your pardon, let me take off my Sonatype hat for just a moment and don that of a general consumer. In this wardrobe change, consider me a consumer of software applications your company produces (which I utilize) or employs (to use your service) - which in both cases it is highly likely I am. Whether it’s newfangled widgets or spacely sprockets, is not important.
Sadly, I’m not well informed, and in some ways I stand now perplexed by the technical world I’ve been dragged through quite inevitably, since birth or some short decades after. It’s scary, and if you listen to the media, it is being made more frightening almost by the day.
Why though?
Back in Character
 Jeff Wayman
Jeff WaymanPlacing my Sonatype hat back on, but leaving the off duty sign lit, I can explain. Well, at least I can postulate on the dark and sinister cloud that things like HeartBleed can bring about.
First and foremost, the media is starting to let consumers of software products know there is cause for concern. Why this is now more prominent news, and not something made pertinent years earlier, could be anyone’s guess. Regardless, the trend will very likely continue.
More importantly, they are making it clear this is something to be paid attention to. While some frequencies may report the detailed and technical accuracy of what’s happening, many are still in heavy perpetuation of an idea that there are highly skilled computer geeks and nerds (nothing derogatory meant by those terms as I lump myself among them as well), working tirelessly in dark rooms to hack all day to get at your personal information.
This is, in and of itself, a truth. This type of thing is happening and can leave a general consumer with a feeling of helplessness. We can more easily rationalize this though. Crime is crime, and there will always be those working within the illegality of things.
What is lurking around the corner though, is that beyond a cloak of coding wizards, is a scarier truth; nearly anyone with a small bit of know-how, and a little perseverance, can use many of the exploits and vulnerabilities known today. These are things that proliferate some open source components, and can be found, literally, everywhere.
The Catharsis Event: Capture the Flag

Eating crow, or being a post-knowledge hypocrite, I had no idea how easy this was until just a few weeks ago. Sitting in Annapolis, Maryland at the annual Sonatype Engineering Conference, I secretly dreaded an item I had seen on the agenda for at least two days now, we’d be conducting a “hacking” exercise commonly know as “capture the flag.” Doing no justice to how I really felt about this activity, there was a bit of nervousness around how effective I would be.
Now, to explain my state of mind, I’m someone that has worked with engineers for the better part of fifteen years. While I’ve dabbled in code, and worked at writing documentation that can be used by engineers, the magic of what they do still confounds me. As such, I keep myself in employ through the alchemy of words, not code.
As we broke into teams, my anxiety heightened. I’d hoped the teams would be larger. That would make it easier to still learn, but not be a flat tire loudly flopping as we attempted to move full speed down the hacking highway; there would only be three. My next holdout was that I might be placed among others of my limited, and as they say, “1337 hackerz skills.” In truth, I think no such others existed.
What unraveled over the next couple hours, was a realization that while there were certainly advantages to development skills, I could do a fair amount of harm with only a small bit of guidance, several easily obtained tools, a big helping of persistence, and “The Internet.”
Exploiting known security flaws in Webgoat, a program co-authored by Sonatype’s own Bruce Mayhew, I was able to complete exercises like finding user names, passwords and credit card numbers. All of these, of course, I should not have had access to. It’s important to remember I accomplished this in minutes, not days or weeks, and I had mostly no experience.
The world of hacking was exposed to me and I became very worried. The fear was no longer corralled by the hope that such things required advanced skills. Some do, most certainly, but there is truth in the ease at which well known exploits can, for lack of a better term, be exploited.
Now, I realize some naysayers will pass this off as exaggeration, but I’ll end with a little story about motivation, the creation of things, and life’s new instruction manual, “The Internet.”
Lessons Learned: Pwn’ed by a 9 Year Old
In my house, I have a stepdaughter that is quite enamored with Minecraft. In days when I had more free time, I too enjoyed a session of what I often likened to digital legos. One evening, as dinner conversations go, we were discussing a rumor that there was a way to get to the moon in Minecraft. For the uninitiated one can travel to unimaginable depths and walk endlessly in any direction. Space, life beyond the atmosphere of a Minecraft world, is not possible. Thus, with a small bit of research, I still stand mostly correct - though there will be a rather happy nine-year old if I am ever proved wrong.
In the course of the discussion though, I mentioned that while a voyage to the moon was quite impossible, cross-dimensional transport was most certainly a thing. Once there she could interact with all kinds of strange things she likely had never seen before.
Her eyes grew bigger, and she asked how. As it was getting close to bedtime, I explained we’d need to craft it from specific materials, and tomorrow, perhaps after school or before dinner we could work on that. For now, we were happy with a video showing this other, magical place.
The next day, as I got off from work, I was greeted with grand excitement.
“Jeffrey!” she exclaimed, “I found the other dimension.”
Now I was puzzled but more interested and asked how she’d performed such a feat without a master wizard of Minecraft (read, me). To which she simply replied, “I looked it up.”
Driven by a heavy dose of motivation, having a set of simple tools at her disposal, and employing the internet as her endless instruction manual, she’d in a way, done nearly the same thing I had done in a capture the flag exercise, no wizards needed.
Retrospective
It’s been a couple weeks now since these events, and I still tell the story almost everywhere I go. To some degree there is a sense of accomplishment that I unraveled something previously quite mysterious. With this revelation, I’ve become a different kind of evangelist within my circle of similar laypeople, not only for what Sonatype produces to directly resolve these issues, but to dispel myths that I had wholeheartedly believed and perpetuated myself.
That’s not to say, when time permits, I’m not also furiously working on a bootstrap space program in the far reaches of a little instance of Minecraft, as I most certainly am, or rather we most certainly are.