This article is another in a series of articles associated with our Executive Brief. To access the executive brief, “Addressing Security Concerns in Open-Source Components,” visit www.sonatype.com/securitybrief. You can follow the conversation on Twitter using the hashtag #OSSsecurity.
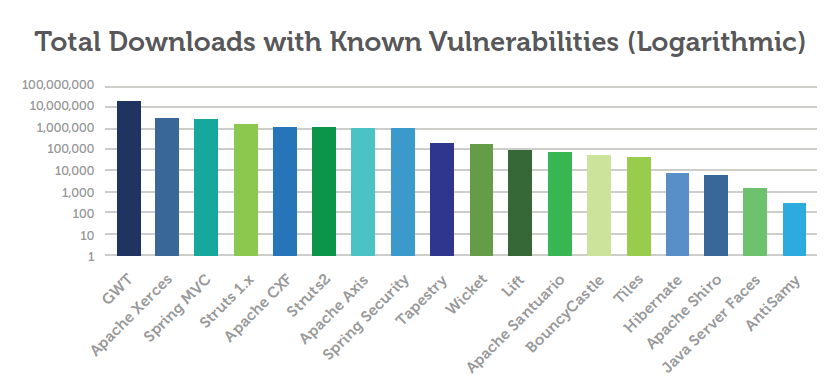
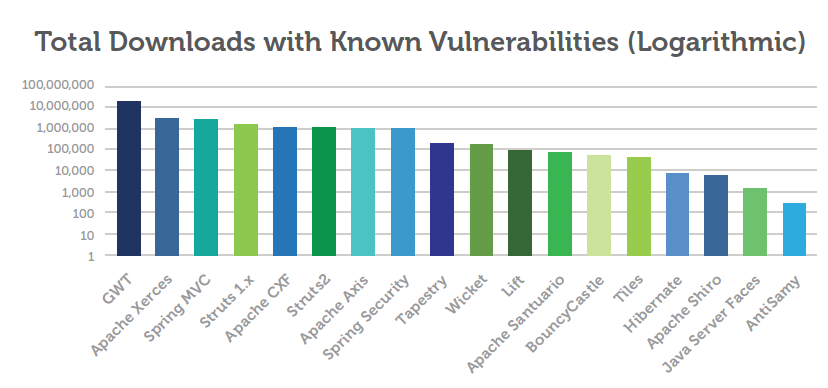
I just wanted to reiterate the key point of yesterday's security brief which is: "You and everyone else in the world are likely downloading vulnerable components." If you don't believe me, then take a look at this graph:
First, note the logarithmic scale - downloads over an entire year. Then, take a look at the left-side of the chart. See anything familiar? GWT, Spring, Struts, CXF, Xerces? If you use these components, you should try to identify which versions are affected by widely known CVE vulnerabilities. It's that simple, if you use these components it would be a good idea to browse the CVE database, or to take a look at Nexus Professional's Repository Health Check.
Really, attackers aren't going to go to the trouble...
Developers, you might be thinking, "an insecurity in GWT or Xerces, who's going to trouble of doing that much research? Who's *really* going to hack into Megabank via some obscure AJP vulnerability in a Tomcat connector?" And if you are asking these questions as a way to shuffle this all under the rug, I understand. There's enough work in the pipeline already and you don't need another thing to worry about. As developers we're not going to turn into security professionals overnight, but we can start using tools like Nexus Professional to help identify vulnerable components and isolate us from deploying known security problems to production.
It isn't the likelihood that someone will hack GWT that is the issue, it is the idea that deploying any code with a known security vulnerability needs to be identified as a disqualifier. The idea that if you get compromised and someone realizes that it was a known vulnerability (for years): developers need to be motivated to avoid this embarrasing situation. The point I've tried to make on this blog is that we (developers) are not really paying attention to this problem because we just assume that it is someone else's problem.
Ignoring Security: It isn't a question of if you'll get hacked, it's when
The issue of data and systems security has repeatedly been front-page news time and time again over the past year. Groups like Anonymous and Lulzsec made a public sport in 2011 of hacking into serious organizations and making every effort to embarrass and ridicule them for lax security. The last few years have been pretty embarrassing years for a lot of security departments at large corporations and a few governments. 2012 promises to be even more active with McAfee predicting the reorganization of Anonymous, but focusing on these high-profile, news-generating events ignores the scope of the problem. It isn't about volume, it is about your exposure to this risk.
I've seen some recent attacks in action. Attacks on both Java-based web architectures and PHP-based architectures. While it's true that PHP-based applications present a much larger and more insecure surface area to attack, it has to be said that Java-based web applications and .NET present a much more lucrative target. An attacker can compromise all the two-bit Drupal instances in the world without stumbling upon anything worth intruding, or they can focus on a multi-month strategy of social engineering and direct attacks to compromise one the Global 100 financial institutions that are downloading insecure dependencies every day.
Welcome to the Security Theater
If you are banking on the fact that attacking Struts 2 or Log4J is just too esoteric for most hackers to do, you are participating in something Bruce Schneier calls Security Theater, and that's really what I'm taking away from this study. Some of these institutions are so invested in presenting an image of trust and security that they will spend millions on Super Bowl ads and marketing efforts to purchase customer trust. But, at the end of that day they continue to download vulnerabilities. It doesn't match up, we need a change of culture in development and security needs to be top of mind.
It's time for developers to start taking security seriously. You could choose to be proactive about the problem and use tools like Nexus Professional to automatically correlate CVE vulnerabilities from CERT with your artifacts, or you can wait until someone replaces your company website with a funny picture and lose the ability to download artifacts from Central altogether. The choice is yours.