Sonatype's automated malware detection bots have caught 86 npm packages that are named after popular NodeJS and JavaScript functions.
The development follows last week's discovery of over 400 malicious npm packages targeting Azure, Uber, and Airbnb developers — all caught by our malware detection system, offered as a part of Sonatype Repository Firewall.
What the Rukkaz?
This week, we discovered seven dozen packages, each published by a different, unique npm account that appears to have been automatically generated using a script:
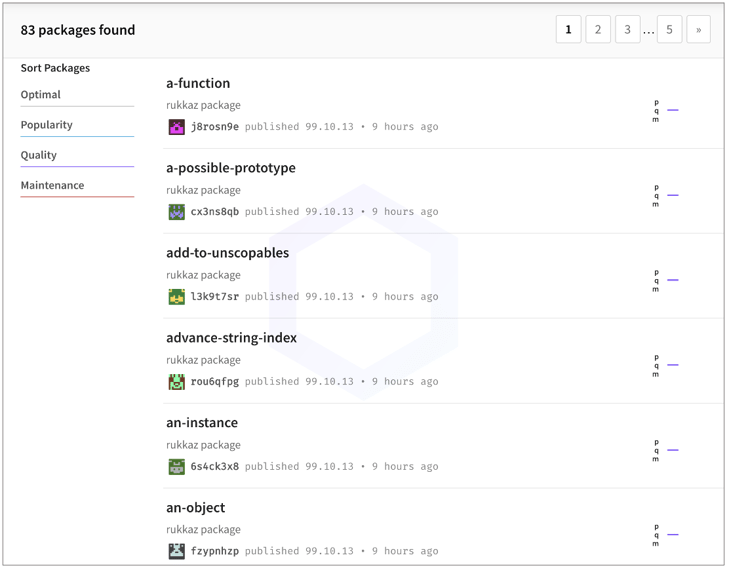
Each package is named after commonly used NodeJS functions, classes, or libraries. Some examples include, 'document-create-element', 'array-iteration', 'an-object', etc.
The complete list of these packages is provided here: page 1, page 2, page 3.
Although all of these packages were published from different npm accounts and contain empty README files, the common factor between all of them are the strings: "rukkaz package" or "azbit package" present in the metadata:
Like last week's campaign, some of these packages, such as 'rush-lib' (mimicking the real @microsoft/rush-lib), target Azure developers and contain identical code for exfiltrating basic system fingerprinting information, such as your IP address, hostname, username, etc.
What does stand out is the mention of terms "Rukkaz" and "Azbit."
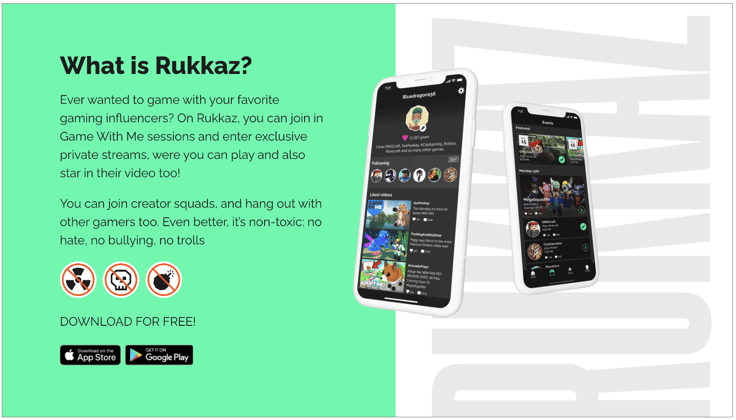
Launched in 2019 by SuperAwesome, Rukkaz is a kid-safe streaming platform that lets players connect with gaming influencers:
And "Azbit" is a fairly popular cryptocurrency exchange with over 350,000 users and a daily $240,000,000 trading volume.
Sonatype is yet to see direct evidence of private dependencies with these names being used by any of these major services. At this time, it seems like a leap of faith on the attacker's part looking to target these firms.
Code won't execute on select systems
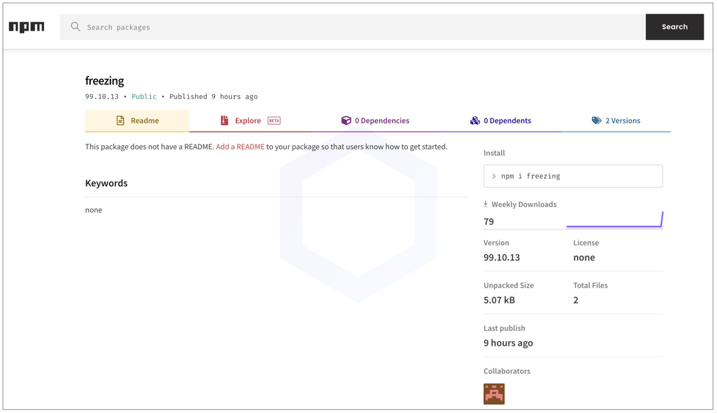
Like thousands of dependency confusion packages seen by us so far, all of these 86 packages exist as "99.X.X" versions and contain identical code. The packages exfiltrate basic fingerprinting information to the attacker's server on 425a2.rt11[.]ml.
But, in an interesting twist, the code contains roadblocks and will kill itself on select machines. For example, if your computer's hostname is set to 'DESKTOP-4E1IS0K', with the username set to 'daasadmin' and the current working directory being 'D:\Transfer\', the code will cease to execute further.
There are additional similar roadblocks in the package to kill execution if certain conditions are met:
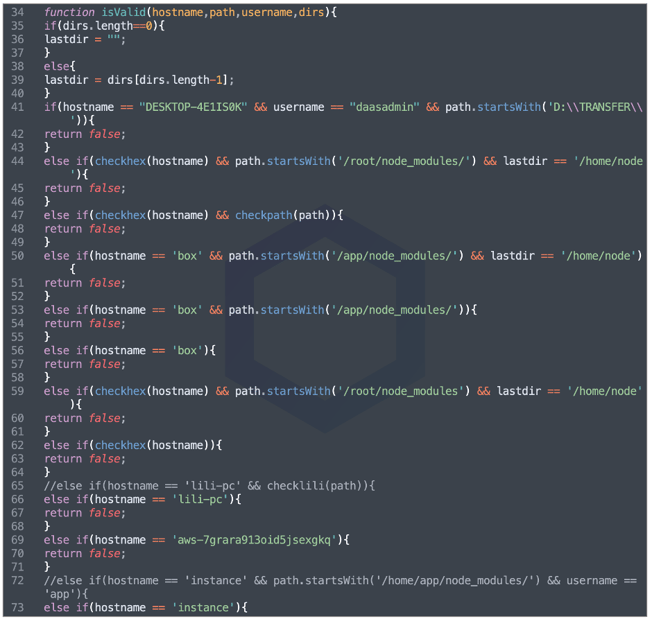
We believe the authors of these packages added such simple checks to prevent the accidental execution of these packages on one of their own systems.
Sonatype reported these 86 packages to npm and these packages were removed promptly by the npm security team prior to our publication of this report.
Sonatype Repository Firewall users remain protected
Users of Sonatype Repository Firewall can rest easy knowing that such malicious packages would automatically be blocked from reaching their development builds.

Sonatype Repository Firewall instances will automatically quarantine any suspicious components detected by our automated malware detection systems while a manual review by a researcher is in the works, thereby keeping your software supply chain protected from the start.
Sonatype's world-class security research data, combined with our automated malware detection technology safeguards your developers, customers, and software supply chain from infections.






