The developer stands at the computer, surrounded by lines of code displayed on the screen. Just like a chef in a kitchen, they have their own "mise en place," a collection of tools and resources organized and at the ready.
The developer moves with the same careful attention and purpose as a chef, carefully combining various "ingredients" of packages, libraries, and frameworks, customizing them to their specific needs to cook a meal of gourmet code.
As they work, they constantly test and taste, making small adjustments and tweaks to the "recipe" of their software application. When satisfied with the results, they serve up their creation to the world, just as a chef presents a perfectly plated dish to a hungry customer.
A recipe of practices for higher quality code
Whether you are a developer of applications or a chef of entrées, you almost definitely work primarily with components created, packaged, delivered, and maintained by other people. Approximately 85% of every application is open source software. In-restaurant or at-home chefs gather most of their ingredients from third-party vendors or stores.
Ingredients and open source software components both come from elsewhere thus both contain inherent reliance on external factors such as:
- Safety and quality of each component
- Ability to track the supply chain of each component
- Knowledge of conflicts or risks in using certain components together
Be it in your IDE or your mise en place, these components exist as your dependencies.
Just like how a chef must carefully manage the ingredients and set up a recipe, you must carefully manage the dependencies in your software project. In this blog post, we'll cover a few best practices to help save you time and better manage whatever ingredients you work with in your project.
Monitor dependency vulnerabilities
A chef starts by carefully selecting and monitoring the ingredients used to make dishes to verify their form and functional profile. The same is true for software developers when it comes to choosing and managing dependencies.
To monitor your dependencies for vulnerabilities, there are a few proactive steps you can take:
- Track the dependencies you use and their versions. This will make it easier to identify when an update is available or if there are known vulnerabilities in the version you are using.
- Map out your dependencies in a consumable, shareable resource such as a software bill of materials (SBOM).
- Regularly review and update your dependencies. Make sure you use the most stable versions of your dependencies, and consider using a tool that can automate this process for you.
Scanning methodologies also help you better monitor your dependencies and find and remediate vulnerabilities.
Just like how a chef begins with ingredients free of contaminants, a developer must ensure their dependencies are free of vulnerabilities and upgraded to the safest, most stable version. And like the rate at which ingredients spoil, software components don't age like fine wine, they age more like milk— good for a while, but when it goes bad you'll have to replace it very quickly.
Use a dependency management tool
The right tool makes all the difference in the kitchen. The same is true for developers when it comes to managing dependencies.
As noted in our latest State of the Software Supply Chain report, “Dependency management tasks are often derided in the development community and colloquially referred to as Dependency Hell.”
But dependency management doesn’t need to be synonymous with a trip through Dependency Hell.
Tools such as Maven, Gradle, or npm can help you more easily manage the libraries and frameworks that your application depends upon. These tools allow you to specify the dependencies your application needs in a single file, which they use to automatically handle downloading and linking the dependencies for you. However, this process will not streamline vulnerability management in your dependencies, and you will still need to check public vulnerability databases.
For an automated approach, Sonatype Lifecycle enables you to choose components based on project quality, ease-of-upgrade, and advanced knowledge of abnormal committer behavior.
Lifecycle saves you time and helps scale your open source security monitoring by:
- Automatically detecting and fixing open source dependency vulnerabilities
- Integrating security vulnerability tools into git repositories you already use
- Avoiding attacks through scaled secure development practices across Dev and Ops teams
Similar to the simplicity of a knife to chop vegetables or a mixer to blend ingredients, a developer can use a software dependency management tool to streamline the process of managing dependencies and customizing them to fit their needs for a specific project.
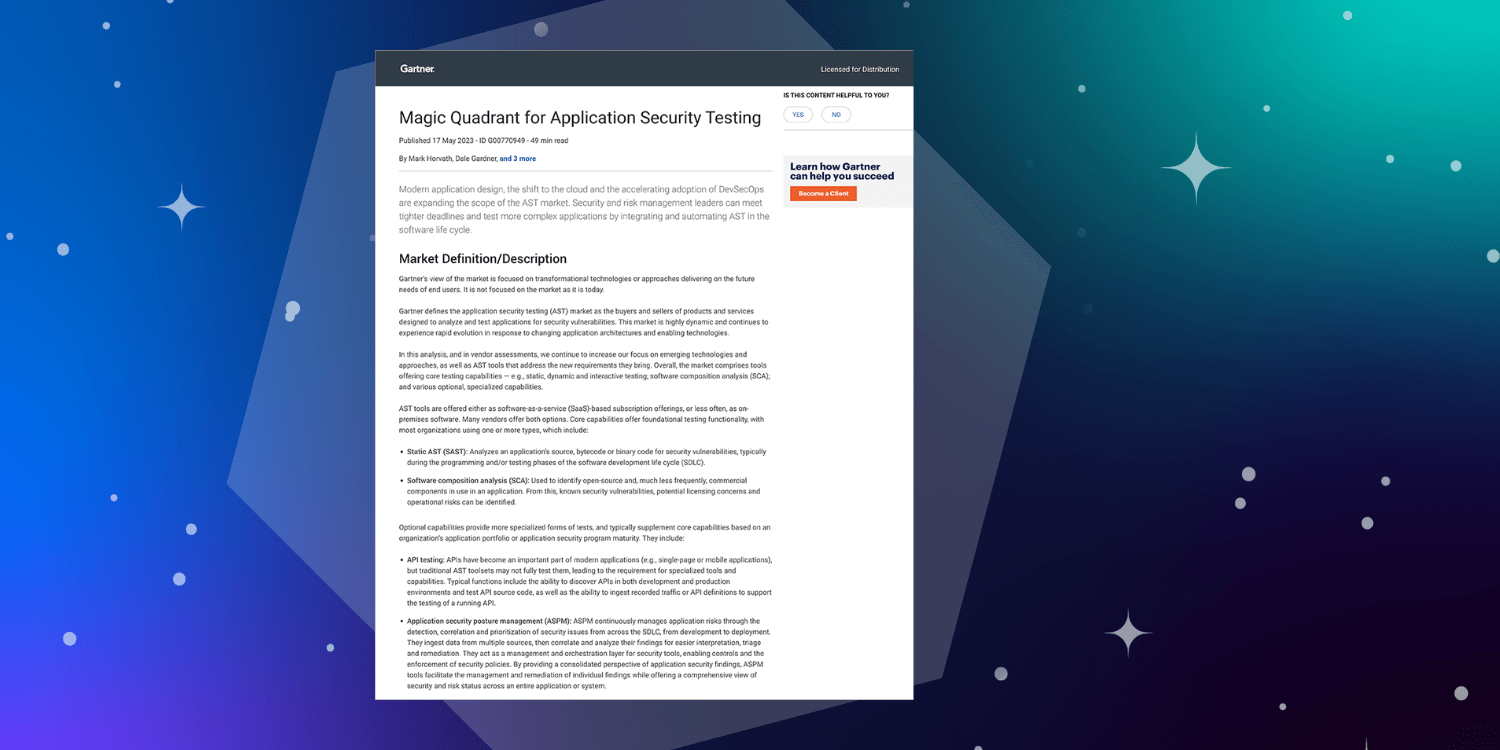
Choose higher quality open source software components
To avoid stale dependencies and minimize security risks associated with third-party open source, consider a project’s quality metrics, such as a mean time to update (MTTU) value and OpenSSF Security Scorecard.
As discovered in our 2021 State of the Software Supply Chain report, MTTU (a measure of a project’s dependency update velocity) is strongly associated with improved project security. Upgrade responsiveness is particularly important when it comes to resolving security issues with transitive dependencies. We created the Sonatype Safety Rating based on the findings.
Some kitchen tools, like food storage aids, can dramatically improve a chef’s ability to deliver high quality food. Similarly, some code-quality analysis solutions evaluate code you own and code you borrow.
Better manage your ingredients for better form and function
Managing software dependencies is an essential part of building and maintaining a healthy codebase. A chef combines the best ingredients with the best tools to create a delicious meal. A developer creates a successful software project with the right dependencies and the right tools.
When you monitor dependency vulnerabilities, pick the right tool, and choose higher quality components, you can ensure that your software project effectively manages security risk and is as healthy as a well-crafted dish.