The Log4j vulnerability may not have changed everyone's world, but it certainly provided an end of year wake up call for the entire software development world. Notably, it's highlighted that critical systems are more than just connections and software. They are software components. As more and more customers have crucial software projects in development within their organization, these vulnerabilities are an ongoing concern.
To help find and resolve issues, Sonatype Lifecycle includes tools to quickly integrate with source control management (SCM) systems such as GitHub, GitLab, Bitbucket, etc. This integration helps avoid open source risk and maintain effective governance down the road. And, it is especially useful for enterprise organizations with an extremely large number of applications who need to find Log4j - or any vulnerability - quickly.
Rapid onboarding
Sonatype Lifecycle customers can use Easy SCM Onboarding to connect to repositories and create Lifecycle Applications from an SCM system. See how to get started below.
 Easy SCM Onboarding Introduction Video
Easy SCM Onboarding Introduction Video
Currently, Easy SCM Onboarding is designed to quickly onboard, configure, and scan up to 15 applications at a time. This enables rapid visibility into open source risks for critical applications.
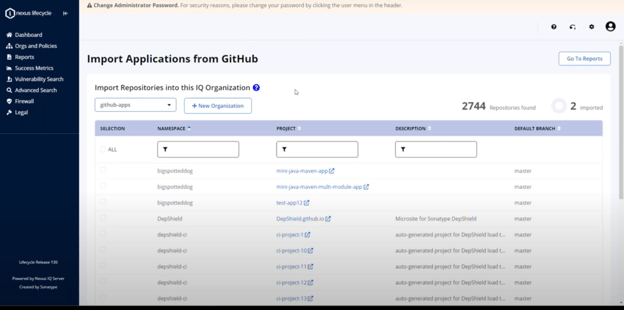 Easy SCM Onboarding import screen
Easy SCM Onboarding import screen
Once created, the applications are automatically scanned for issues, including problematic Log4j components.
Source analysis
As new applications are onboarded, Instant Risk Profile feature performs source control evaluations. As the name implies, this provides immediate feedback on source code issues, as well as ongoing assessments.
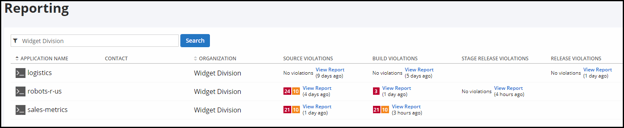 Instant Risk Profile screen
Instant Risk Profile screen
With it, teams can begin to identify vulnerabilities in direct dependencies that show up explicitly in a project's build manifest files.
For transitive dependencies, we recommend that you integrate with our Nexus IQ CI, CLI or Maven plugins. These dependencies include those not directly found in a project's build manifest files, but instead required by your direct dependencies.
Best practices
Although every company is different, we've found ways to make large organizations more effective and efficient with Easy SCM Onboarding. Sonatype's recommendations to these customers and partners is detailed below.
- Create multiple organizations. Modifying organizations in IQ Server to onboard the repositories should ideally mirror the structure of your organization. We recommend drawing from team names, departments, or other logical areas (e.g. logistics).
- Create multiple SCM users/tokens. Creating more than one token for use by IQ Server helps overcome some restrictions in the SCM systems themselves, particularly GitHub. It also allows IQ Server to do more work in parallel, delivering faster results. Sonatype's current guidance is to have one SCM user/token for every 500 or so IQ applications, ideally assigning a different one to each IQ organization.
- Over 1,000 repositories? Setup an external database rather than using the embedded H2 database that comes with IQ Server. For details on this process, visit our documentation detailing External Database Configuration.
- Retain the repository discovery results. Discovering the repositories in an SCM system can be a time-consuming process. Once you've reached that point in the onboarding process, we recommend maintaining those results in an open browser as you continue to onboard repositories.
- Divide and conquer. This process is assisted by either multiple users onboarding into different IQ Server organizations, or multiple browser sessions for a single user.
- Set up multiple IQ Server instances, perhaps one for each major part of your organization. This will help keep each individual IQ Server instance lean and performant.
In addition to the resources above, Sonatype's Russ Jackson assembled a video series to help you easily set everything up.
Note that these videos are best viewed in the order listed below.
- Introduction / prerequisites
- Configuration settings
- Optimizing the onboarding experience
- Viewing and searching instant risk profile results
- Planning and implementing the organizational structure
- What's next?
Getting your SCM repositories integrated with source code scanning tools can save time, effort, and frustration, especially when you need to scan thousands of applications. Address open source risk by identifying and remediating Log4j and other issues using Sonatype Lifecycle.