Just like a car manufacturer must ensure every component that goes into their vehicles is safe and reliable, you should ensure all of the components in the software you produce are secure and free from defects, especially with software supply chain attacks on the rise.
But it's not just attacks that should get your attention. Producing secure software is becoming a central concern of governments around the world. This includes policy and regulation to ensure your organization can:
- safely procure (open source) software;
- securely develop and release software applications; and
- quickly identify and mitigate security risks.
If this sounds challenging just to get started, and even more so at scale, you aren't alone. Many organizations are trying to navigate these issues and improve the security of both their software development processes and software supply chains.
So how do you adjust your organizational approach to secure software development?
A good first step could be to build a foundation on best practices and recommendations, allowing your development team to better manage risks in your software supply chain.
You could dive in and build your own processes to improve the security of your software supply chain. However, a better strategy would be to utilize existing software security frameworks and tools.
What is a software security framework?
A software security framework is a set of standards and suggested practices your organization can follow to better secure your organization’s approach to software development. In many cases, frameworks consist of researched and tested best practices tailored to meet rigorous certifications or requirements.
In the case of software security frameworks, the primary goal is to help developers manage security risks associated with software development. However, with the modernization of these frameworks, many now incorporate recommendations to minimize and mitigate risks associated with open source software (OSS) vulnerabilities and in turn improve software supply chain security.
A framework that prioritizes the security of your software supply chain can include these processes:
- Manage your dependency stack
- Scan for vulnerabilities
- Leverage security testing tools
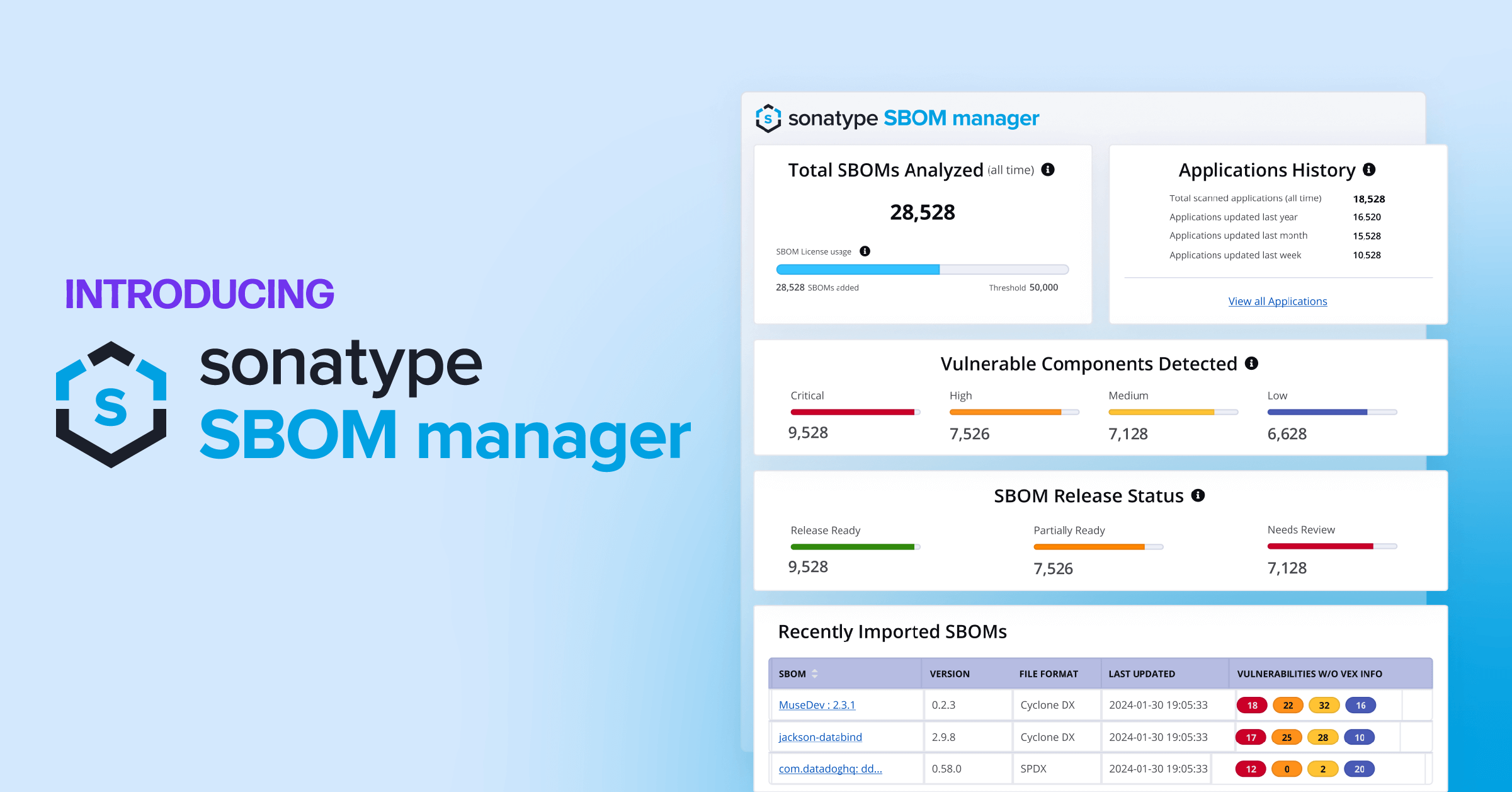
- Start using software bills of materials (SBOMs)
A software security framework differs from cybersecurity frameworks, such as SOC2 and ISO 27001, in that it focuses specifically on software development processes. In contrast, cybersecurity frameworks provide a broader set of guidelines and best practices to protect an organization's assets, such as infrastructure, hardware, and cloud services.
Software security frameworks represent a return to fundamentals to ensure every aspect of software development matches secure, accepted best practices. This may include approaches to provisioning access to key development systems, but it also provides guidance to fix the code you have and make better decisions about your consumption and use of open source software.
Why use a software security framework?
A software security framework provides you with a holistic approach to:
- improve decision making in development processes;
- build a stronger defense against bad actors; and
- prepare for incoming government policy and regulations.
The changing landscape of government regulation and software liability is enough to drive any software organization towards change. However, you should want to release secure software as a commitment to the quality and security of your products for your customers.
Implementing a software security framework can help you adopt more secure development processes with a focus on shifting security left in the software development life cycle (SDLC). For example, by integrating security into the development process from the earliest stages, you can help reduce the risk of vulnerabilities associated with open source software.
This includes defense against software supply chain attacks, which are becoming more prevalent and sophisticated, and requires an organizational approach. These attacks exploit vulnerabilities or inject malware into your software supply chain. By attacking components in your software supply chain, bad actors infiltrate not only your organization but your customers as well.
Due to the prevalence of these attacks, governments have begun soft-launching regulations to put liability on software manufacturers working with the public sector to better secure their software supply chains. This includes using SBOMs, adopting best practices for vulnerability disclosures and responses, and building secure-by-design products which CISA describes as “products where the security of the customers is a core business requirement, not just a technical feature.”
By following the guidance provided in a software security framework, organizations can ensure compliance with these regulations and avoid penalties or other consequences. And as the government rhetoric increases, soon it will no longer be a choice whether or not you want to secure your software supply chain.
How does a software security framework help you?
Tactics, policies, and procedures vary based on how you choose to implement a software security framework. In the context of your software supply chain, a software security framework helps you:
- see what’s inside your applications and better understand your software supply chain as a whole;
- empower your developers to make better decisions in selecting components; and
- scale your secure practices.
A consistent principle found in software security frameworks is the ability to track what’s inside your applications. Knowing what’s inside your applications requires implementation of SBOMs and utilization of software composition analysis (SCA) tools to provide visibility into the OSS components you consume and use in your applications.
Once you have visibility into the OSS components, the next step is to funnel information to your developers so they can make better-informed choices to navigate vulnerabilities, licensing, and other factors related to the consumption of OSS. This can involve implementation of policies that govern the procurement and use of components and additionally for vulnerability scanning, testing, and the use of signed software components.
To be effective, a software security framework needs to be implemented at scale. This involves prioritizing the most critical components, establishing firm policies, and monitoring the process from an enterprise-wide perspective. This can be achieved through use of automated tools and processes, such as continuous integration and continuous delivery (CI/CD) pipelines, which can help ensure your software supply chain is secure at every stage of the SDLC.
At this point the framework has provided a canvas. The final step is to continuously monitor, iterate on, and improve the security of your software chain. This involves regularly reviewing policies and procedures, updating vulnerability databases, and incorporating new tools and technologies as they become available.
What are a few examples of security frameworks?
Here are a few examples of existing frameworks and elements that can help incorporate more security into a software supply chain. In the future, we’ll take a deeper dive into each one of these and look at specific recommendations they provide for securing your software supply chain.
NIST SSDF
The National Institute of Standards and Technology (NIST) Secure Software Development Framework (SSDF) is a set of guidelines and best practices for integrating security into the SDLC. NIST developed this framework in cooperation with industry experts to establish a more structured approach to developing secure software.
The framework consists of three main categories: Prepare, Protect, and Respond, each with a set of specific activities and references for building and deploying secure software. By using the SSDF framework, organizations can develop a more secure SDLC and reduce the risk of security incidents.
BSIMM
The Building Security In Maturity Model (BSIMM) is a framework for assessing and improving an organization's software security practices. Based on data collected from over 200 organizations and developed by a group of security professionals in 2009, BSIMM consists of specific activities and best practices distilled into 12 categories including strategy and metrics, compliance and policy, training, and code review. This framework exists as a benchmarking tool to help organizations improve their security programs and reduce the risk of security incidents.
NIST C-SCRM Practices for Systems and Organizations
The NIST Cybersecurity Supply Chain Risk Management (C-SCRM) Practices for Systems and Organizations provides a set of guidelines to help organizations identify, assess, and manage security risks that can arise from their use of products and services by external suppliers.
The framework consists of the Core, Profile, and Implementation tiers and covers topics like vendor selection, ongoing monitoring, and incident response. The framework’s guidelines intend to be adaptable to different organizations and can be used to develop effective software supply chain risk management programs.
Executive Order 14028
United States Executive Order 14028, also known as “Improving the Nation's Cybersecurity,” is an executive order signed by President Joe Biden in May 2021. The order aims to strengthen the cybersecurity posture of the US government and private sector by establishing new guidelines and requirements for federal agencies and technology service providers.
The order includes several key provisions, such as the following:
- Improve information sharing about cybersecurity threats and incidents between federal agencies and private sector entities.
- Establish baseline cybersecurity standards for federal agencies and require them to adopt multi-factor authentication and encryption.
- Require federal contractors to meet new cybersecurity standards when providing products and services to the government.
- Develop a standard cybersecurity incident-response playbook for federal agencies.
- Modernize federal cybersecurity infrastructure and practices.
- Create a Cyber Safety Review Board to review and assess significant security incidents.
The order represents a coordinated effort to address growing cybersecurity threats. It’s already had far-reaching implications for government agencies, federal contractors, and technology service providers that work with the US government.
OpenSSF Scorecard
This scorecard is an open-source self-assessment tool developed by the Open Source Security Foundation (OpenSSF) to help organizations evaluate their security practices and identify areas for improvement in their software supply chain security.
The scorecard is not a framework in the spirit of the previous example. However, it can help organizations identify potential security gaps and prioritize security investments. By completing the self-assessment, organizations can gain insights into their security posture and identify areas for improvement. The scorecard provides guidance on how to address any identified gaps and improve overall security practices.
Additionally, the OpenSSF scorecard can help organizations demonstrate their commitment to secure software development practices and software supply chain security to customers, partners, and stakeholders. By publicly sharing the results of their self-assessment, organizations can provide greater transparency into their security practices and demonstrate their commitment to improving software security.
Moving beyond a software security framework?
The security of the software you produce is just as important as its functionality. A software security framework is crucial for ensuring software development teams are equipped to manage the security risks associated with using open source software. This means developers are empowered to make better decisions when selecting components, teams have improved visibility into the OSS components they use, and organizations are prepared to better manage the security risks associated with their SDLC.
However, this is just the first step. Real improvement to the security of your software supply chain is accomplished over time. Software security frameworks represent a foundation to build more mature processes. As a result, organizations that implement software security frameworks will be better positioned to adopt more secure software development processes, mitigate risks associated with software supply chain attacks, comply with incoming industry regulations, and ultimately release more secure software for their customers.
In future posts we will dive deeper into each of these frameworks and review key recommendations for improving software supply chain security. We’ll share insights from Sonatype’s Software Supply Chain Maturity Framework that help assess and guide organizations on their journey to improved software supply chain security.