Today, we announced extended support for RubyGems and RPM components within Nexus Firewall. This means that every RubyGems and RPM component downloaded from public repositories is evaluated for license, security, and other risks. Nexus Firewall allows good components through, and bad components get stopped and quarantined at the front door. Nexus Firewall also supports this same capability for Java, .NET, npm, and PyPi components.
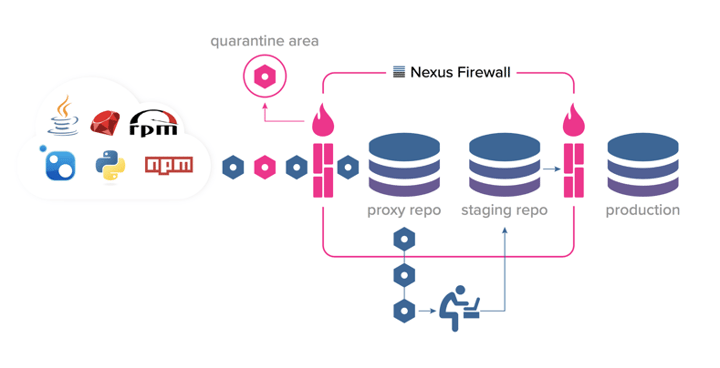
Our data research team identified over 34,000 vulnerabilities within RubyGems and RPM components - making it nearly impossible for DevOps teams to manually determine which ones are good and which ones are bad. With Nexus Firewall, open source governance policies are automatically evaluated when proxying public repositories to quarantine components that don’t comply with policy.
With GDPR right around the corner and in light of recent security breaches, it is important to shift security practices left. Nexus Firewall integrates automated security into the earliest stage of a DevSecOps pipeline to ensure organizations build applications that are secure by design.
Watch this video to see how it works and reach out if you want to learn more.