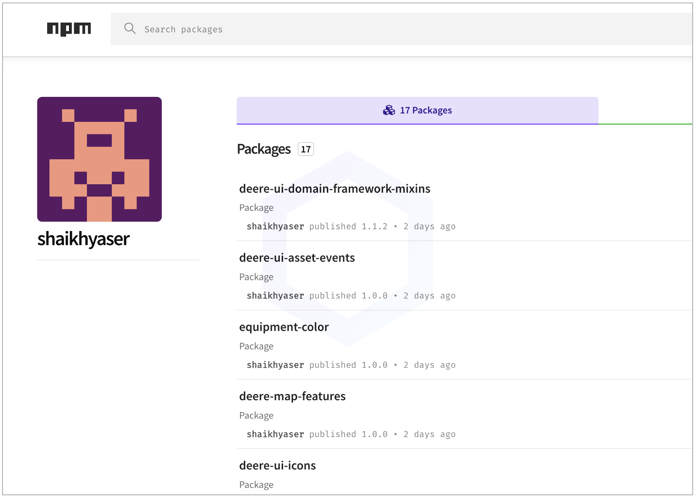
This week in malware we discovered and analyzed 17 packages, at least a dozen of which were dependency confusion PoCs directly targeting the agricultural equipment giant John Deere (Deere & Company).
Additionally, we discovered 40+ PyPI and npm packages that are either dependency confusion candidates, prank packages, contain PoC reverse shell code, or were otherwise flagged as suspicious for containing extensive obfuscation without good reason.
John Deere dependency confusion attempt flagged by Sonatype
John Deere, or more specifically, Deere & Company, is a U.S.-based global producer of agricultural equipment including machines, tractors, and engines, as well as provider of financial services.
This week Sonatype identified 17 npm packages, at least 12 of which directly target John Deere's private npm dependencies via dependency confusion, a technique that continues to repeatedly be employed by bug bounty hunters and malicious actors alike when targeting open source packages.
Read the dedicated blog post to learn more.
More suspicious and malicious packages
npm and PyPI packages flagged as suspicious or malicious by our automated malware detection bots are listed below:
@capire/bookstore
@capire/reviews
astar-portal-test-depconf
axelar-signing-relayer
bitmovin-internal
chat-orion-sdk
defi-interfaces
defisaver-v3-contracts-test
elementor-developers-docs
ember-addon-with-dependencies
employers-routes
gather-electron-interop
hft-frontend-test
jworkflow
kadenaswap-ui
lido-cosmos-docs
lido-dao-test-dp
maliciouseuropy
malpip-tgh
monash-college-combo-box
notion-intl
owncloud-guests
peekatchuysharmlesspackage
pratikyadavpack
route-sonar
st6
st7
starlink5
stripe-demo-connect-standard-saas-platform
tbgo6
tbgo7
tolbichgo
tolbichgo1
tolbichgo3
tolbichgo4
twilio-bugcrowd-poc-twilio-flex-ui-sample
wm-accounts-auth
wm-accounts-auth-core
wm-accounts-sdk
wm-dagre
wm-ngx-graph
wm-shared-consts
Turn on Sonatype Repository Firewall for automatic protection
This discovery follows our earlier report of malicious Python packages that stole Telegram cache files and set up illicit Remote Desktop (RDP) accounts on Windows systems.
As a DevSecOps organization, we remain committed to identifying and halting attacks against open source developers and the wider software supply chain, like the ones discussed above.
Users of Sonatype Repository Firewall can rest easy knowing that such malicious packages would automatically be blocked from reaching their development builds.

Sonatype Repository Firewall instances will automatically quarantine any suspicious components detected by our automated malware detection systems while a manual review by a researcher is in the works, thereby keeping your software supply chain protected from the start.
Sonatype's world-class security research data, combined with our automated malware detection technology safeguards your developers, customers, and software supply chain from infections.






