This week in malware, highlights include malicious npm package 'flame-vali' that claims to let developers "bypass any request proxys." But that's not quite the case. And, some more dependency confusion packages caught by us.
npm package attempts to kill Windows Defender
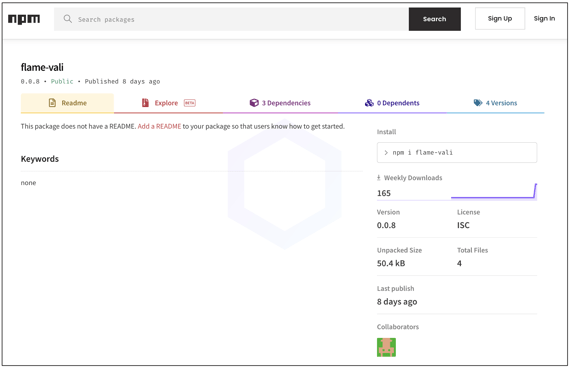
Caught by Sonatype's automated malware detection systems, npm package 'flame-vali' contains heavily obfuscated JavaScript that makes multiple attempts to disable Windows Defender.
Sonatype security researcher Carlos Fernandez analyzed the 'flame-vali' package which has been assigned sonatype-2022-3346 in our security research data.
Check out the dedicated blog post to learn more.
Python devs using AIOHTTP repeatedly targeted
We have previously disclosed counterfeit PyPI packages imitating legitimate libraries like AIOHTTP and the trend hasn't slowed down, with more such typosquatting malware being published to PyPI:
aiohttp-async-proxy
aiohttp-async-socks
Additionally, the following malicious PyPI packages were reported by us to PyPI this week:
3.number-of-iterations
libdeflate
pygrata-utils
smallmatter
test-test-test123
Dependency confusion packages
This week's list of npm dependency confusion packages caught and reported by us includes:
@atlas-angular/logger
@manomano-toolbox/api-gateway
@manomano-toolbox/async-exports
@manomano-toolbox/catalog
@manomano-toolbox/commercial-operations
@manomano-toolbox/components
@manomano-toolbox/hub
@manomano-toolbox/pim-management
@manomano-toolbox/toolkit
@spinak/iac
@spinak/iac-lib
@tamagoshi/core
@tamagoshi/icons
@tide-web-apps/bert2
@tide-web-apps/global-environments
@za-cli/components-react
agoric-servers
caspr-front
cat-weather-widget
cat-webcomponent-image
email-report
ferris-design-tokens
joax
kaluza-tech
mano-toolkit
mephisto-worker-experience
mimic-server
mmolecule
nab-packages-react-utils-nab
newtestforme1007
newtestforme1008
node-red-contrib-aws-stream-manager
nstmrt
ololo123
perf-benchmarks
react-table-types
react-table-v7
red-contrib-aws-stream-manager
solar-stellarorg-pages
vipps-stitches
vpc-stack-with-issues
vso-ts-agent
vulny-appy
wxy-tools
xo-guest-components
zzzhelloeveryone
Sonatype Repository Firewall users remain protected
These discoveries follow our last week's report on several dozen malicious packages including '@core-pas/cyb-core' that attempts to exfiltrate several sensitive assets from a user's system:
- /etc/passwd
- C:\WINDOWS\system32\config\SAM
- C:\WINDOWS\system32\config\SYSTEM
- Amazon EC2 credentials
Users of Sonatype Repository Firewall can rest easy knowing that such malicious packages would automatically be blocked from reaching their development builds.

Sonatype Repository Firewall instances will automatically quarantine any suspicious components detected by our automated malware detection systems while a manual review by a researcher is in the works, thereby keeping your software supply chain protected from the start.
Sonatype's world-class security research data, combined with our automated malware detection technology safeguards your developers, customers, and software supply chain from infections.





