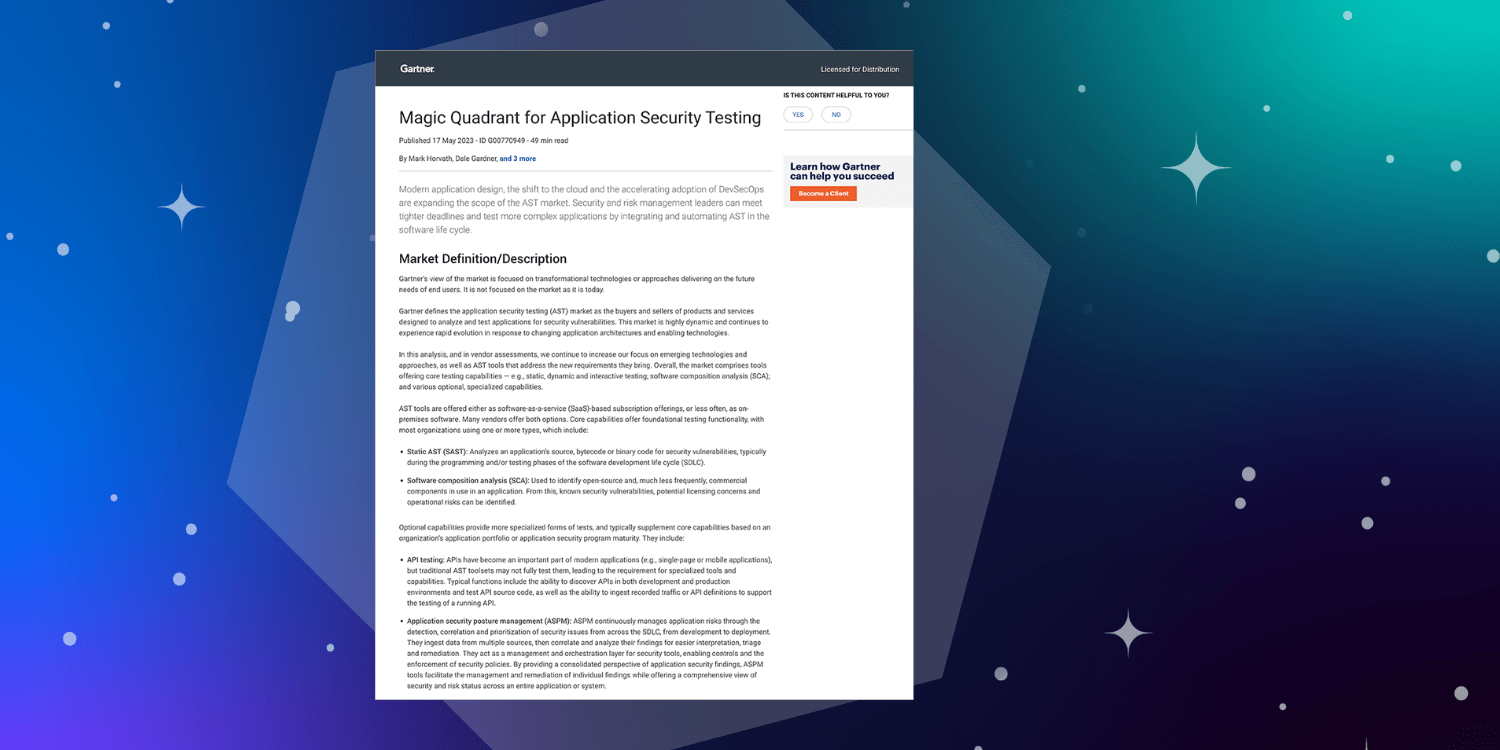
The application security market is saturated with tools like DAST, SAST, IAST, and RASP - which can be overwhelming. Each of these tools play a specific security role within the SDLC, but are they really representative of AppSec risk or just different flavors of traditional methodologies?
When it comes to reducing vulnerabilities within the SDLC and gaining an overall picture of risk, a question we are frequently asked is, “What’s the difference between SAST and SCA?” The short answer: they address completely different problem sets.
Static Application Security Testing (SAST) defined
SAST is a security testing tool that’s been around for over a decade and was developed when most code was proprietary and copy/pasting snippets was a huge problem. Its primary use case is reporting security and quality issues in proprietary, static source code (internally written). This is different from Dynamic Application Security Testing (DAST), which flags run-time issues.
Software Composition Analysis (SCA) defined
On the other hand, SCA is a newer technology solving a different problem - open source governance. SCA supports more modern development environments where software is procured by developers from an upstream supply chain. SCA tools scan applications to identify open source components, creating a software bill of materials (SBOM) and ultimately surface risk using metadata about overall component quality (vulnerabilities, licensing, architecture, etc.). It’s primary use case is compliance and developing dependency management workflows.
SAST vs. SCA - What’s the difference?
When comparing SAST and SCA, it comes down to what they are analyzing, and you can’t really compare the two. SAST analyzes proprietary code while SCA analyzes open source.
- Binaries + Source Files vs. Source code - SAST tools only analyze the source code/compiled code. This can prove problematic for a few reasons. SAST requires access to the source files, and in some cases organizations no longer have access to the source code or they have access to it but it can’t be compiled because it is missing key libraries, and you can’t patch an issue if it is not represented in the code.
Analyzing weaknesses in how code was written will identify many of the OWASP top 10 vulnerabilities, but with 85% of a modern application made up of open source components, this still leaves the majority of the application unscanned for vulnerabilities.
SCA tools scan files and binaries, which provides more coverage for an application. While you could use SAST tools to read through the source code of OSS libraries and identify security flaws, unless you want to make code contributions (and convince the maintainers to accept them), that won’t solve the problem.
Instead SCA tools enable developers to select a better open source version that complies with policy and is also designed to work in a DevSecOps environment. SCA scans are quick and can be embedded within CI/CD to fail builds or even further left in the developer’s IDE or SCM via pull requests to fix open source components that a developer introduced.
- Early vs. Everywhere - SAST tools find vulnerabilities early-on in the development cycle whereas SCA tools provide continuous monitoring for vulnerabilities at every stage of the SDLC. SAST tools can integrate into CIs and IDEs but that won’t provide coverage for the entire SDLC. In order to get full SDLC coverage SAST tools must be grouped with other tools like DAST and IAST to create a comprehensive solution. At its core, SCA is an end-to-end solution, providing continuous open source coverage for the entire SDLC.
- False Positives - Similar to our first bullet, if code is improperly configured, SAST tool scanning will result in a high number of false positives. SCA tools are known for working fast, so suited for releasing early and often, and with a low false positive rate.
Comparing SCA to SAST is kind of like building a house: SCA is analogous to submitting blueprints for a building permit while SAST is like doing an inspection of the house after it is built. Building the house is more complex than inspecting the house after the fact because blueprints:
- Often reference other blueprints that are not under your control
- Include instructions to use items not included in any set of blueprints
- Stipulate how they can be shared and who can access them
- Used by contractors are not always the approved version
Modern DevSecOps teams are struggling to manage these various “blueprints” and require a solution to help them do this at scale.
What’s Best for My Organization?
When it comes down to it, SAST and SCA are really two different types of technologies and are not an apples-to-apples comparison. What we’ve found working with customers is that they typically start with SCA as the majority of their work is with open source, and they have already created some form of open source policy - either manual approvals or a whitelist/blacklist approach - before starting their DevSecOps journey.
SCA becomes ideal for those focusing on making holistic decisions about which third party libraries make up their applications, not individual issues like many S/D/I-AST tools. SCA speeds time to innovation - automating manual open source governance processes that are prone to errors (i.e., policy enforcement) and adding context and awareness around application security.
The bottom line: There is no one-size-fits-all answer, but a best practice is to choose a best-of-breed SCA or SAST solution. One that provides end-to-end coverage, whether you’re working in proprietary or open source code. At Sonatype, we focus on automating open source governance at every stage of the SDLC with precision to eliminate false positives and false negatives and have partnered with a leading SAST provider to analyze proprietary code.
Learn more about key technology considerations when selecting SCA solutions by downloading this Gartner Technology Insight for SCA report.