Over the past year, COVID-19 fundamentally transformed how people live and work, how companies interact with customers, how customers shop and buy, and how physical and digital supply chains function. As the economic importance of digital innovation accelerated during the global pandemic, so too did the number of cyber-attacks aimed at exploiting software supply chains.
And yet, much has stayed the same. Top performing companies like Apple, Goldman Sachs, and Amazon — and more recently, Zoom, Peloton, and Wayfair have mastered three key competitive advantages: knowing how to use open source and third-party innovation at scale, integrating security and risk controls into multiple phases of the software supply chain, and releasing higher quality code faster than their competitors.
After a year of research that involved studying 100,000 production applications and 4,000,000 component migrations made by developers and operational supply, demand and security trends associated with the Java (Maven Central), JavaScript (npm), Python (PyPI), and .NET (NuGet) ecosystems, we’re excited to share the 2021 State of the Software Supply Chain report.
Here's what we learned this year:
Open source supply, demand, and security vulnerabilities have all exploded
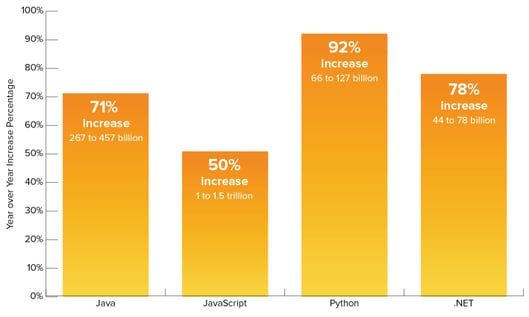
- Supply increased 20%. The top four open source ecosystems now contain a combined 37,451,682 different versions of components.
- Demand increased 73%. In 2021, developers around the world will download more than 2.2 trillion open source packages from the top four ecosystems.
- Open source attacks increased 650%. In 2021, the world witnessed an exponential increase in software supply chain attacks aimed at exploiting weaknesses in upstream open source ecosystems.
- Production apps utilize only 6% of available open source projects. Despite a huge available supply of open source projects, utilization is concentrated in a surprisingly small number of popular projects.
- Popular open source projects are more vulnerable. 29% of popular project versions contain at least one known security vulnerability. Conversely, only 6.5% of non-popular project versions do so, suggesting that security researchers (blackhat and whitehat) are focused on the most utilized projects.
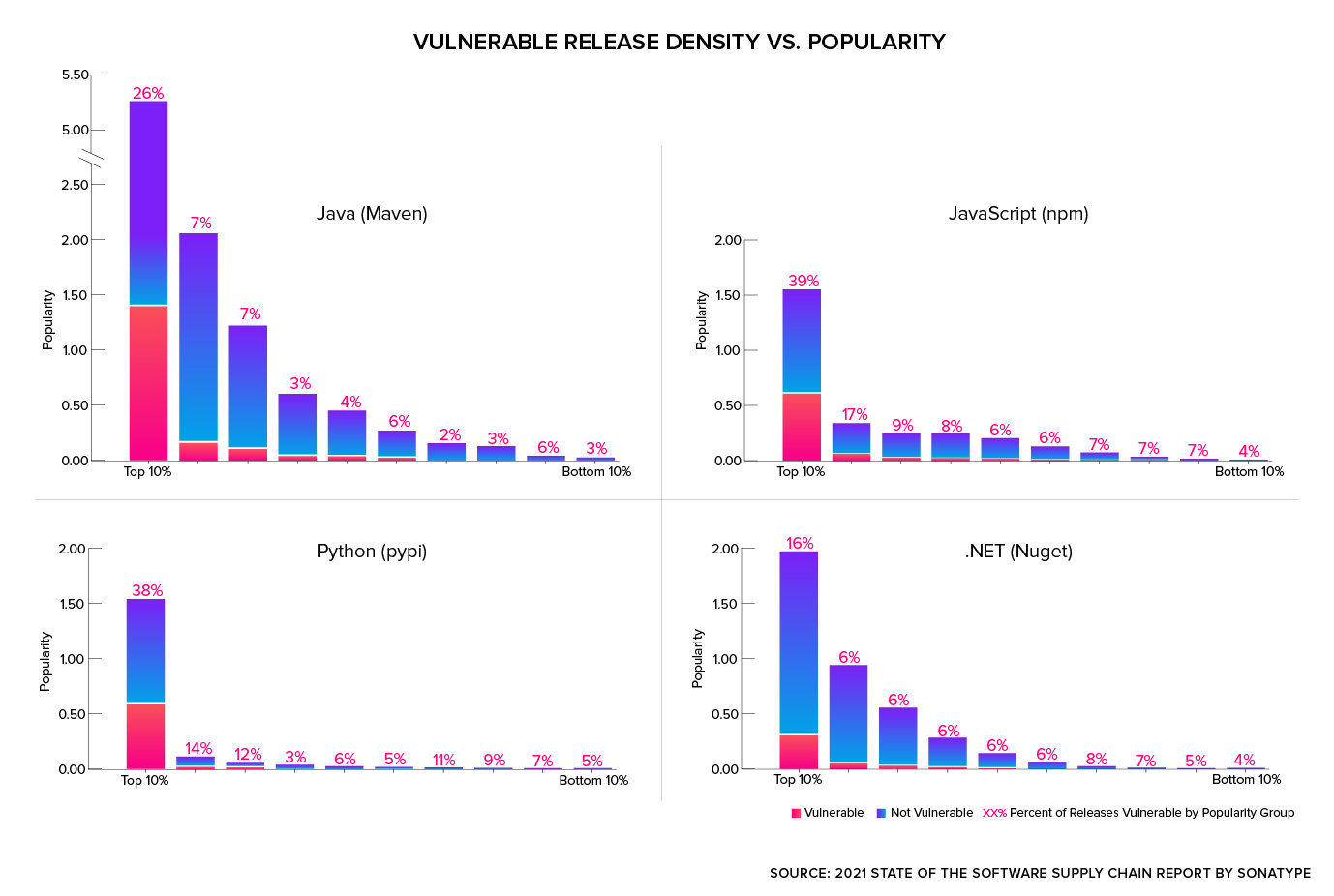
While developer demand for open source continues to grow exponentially, our research shows for the first time just how little of the overall supply is actually being utilized. Further, we now know that popular projects contain disproportionately more vulnerabilities. This stark reality highlights both a critical responsibility, and opportunity, for engineering leaders to embrace intelligent automation so they can standardize on the best open source suppliers and simultaneously help developers keep third-party libraries fresh and up to date with optimal versions.
Some open source projects are better than others
- Projects with a faster mean time to update (MTTU) are more secure. They were found to be 1.8 times less likely to have vulnerabilities.
- Popularity is not a good predictor of security. Popular open source projects were 2.8 times more likely to contain vulnerabilities.
Dependency management practices vary widely among development teams
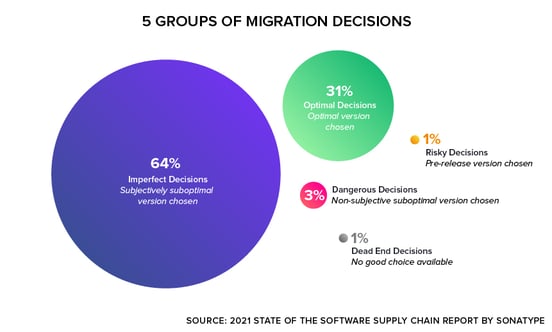
- Software developers make suboptimal choices 69% of the time when updating third-party dependencies. Newer versions of projects are generally better, but not always best.
- Commercial engineering teams only manage 25% of components they use, leaving the majority of their open source dependencies stale and susceptible to increased security risks.
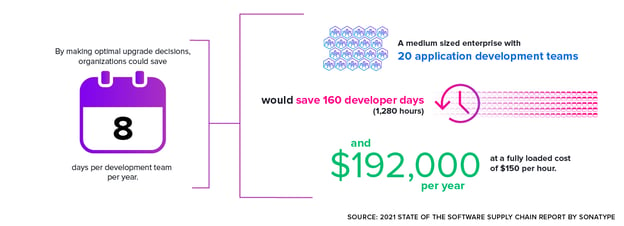
- Automation could save organizations $192,000 a year. Equipped with intelligent automation, a medium sized enterprise with 20 application development teams would save a total of 160 developer days a year.
Software supply chain management practices: Perception vs. reality
- There is a disconnect between subjective survey feedback and objective data. People believe they are doing a good job remediating defective components and indicate that they understand where risk resides. Objectively, research shows development teams lack structured guidance and frequently make suboptimal decisions with respect to software supply chain management.
You can read this year's full report here. For those of you interested in hearing more about our findings, get in touch and we'd be happy to walk you through it one-on-one.