I field a flood of requests every week asking to learn more about Sonatype Auditor. I get it. Sonatype Auditor, in the right use case, is a solid, cost-effective solution.
Is Sonatype Auditor the solution for you? Maybe, maybe not. I thought it would be beneficial to explain who should consider Sonatype Auditor. So here is an example that I received this week.
First, meet Stephen (not his real name). Stephen is a Senior Security Architect who has worked at ABC Corp. for 10 years. Stephen read a Gartner whitepaper about getting started with software composition analysis (SCA). He thinks this type of solution could help his organization better manage risks around OSS components. Even more importantly, he needs a way to verify license compliance.
Like many others, Stephen did his research on Sonatype.com and other competitor sites before reaching out to me. He is now interested in learning more about Sonatype Auditor. Stephen already uses some free tools like OWASP Dependency-Check. However, now that solution is no longer meeting his organization's scalability and tracking requirements.
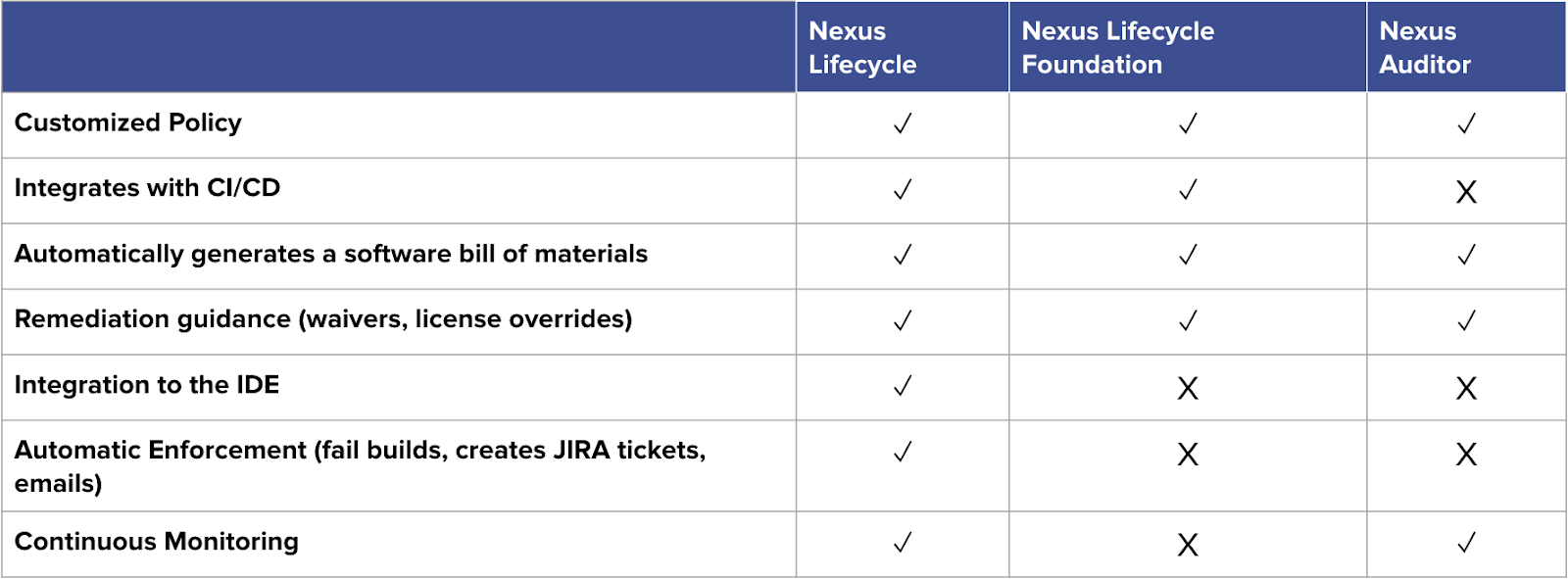
Often people like Stephen are confused about the differences between Sonatype Auditor and Sonatype Lifecycle. Is it right for Stephen? Is it right for your organization? Let's take a look...
Keep it simple
Do I need Sonatype Auditor? Here's a simple flow chart to walk yourself through:
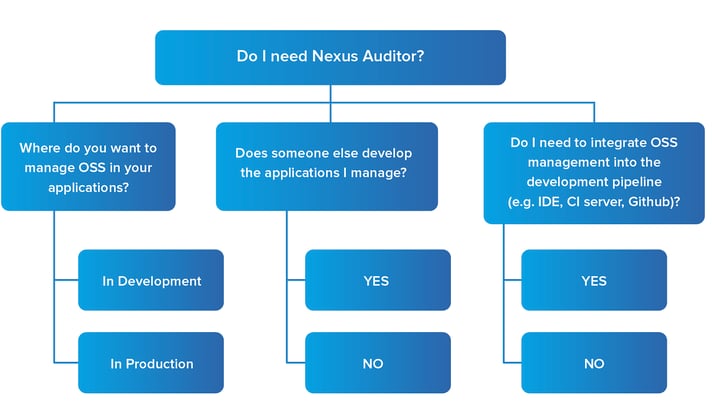
Ask yourself:
Where do you want to manage OSS in your application?
In Development, or in Production?
Does someone else develop the application I manage?
Yes or no?
Do I need to integrate OSS management into the development pipeline (e.g., IDE, CI Server, GitHub)?
Yes or no?
All of these answers will determine if Sonatype Auditor is a good fit for you.
Sonatype Auditor is superb for monolithic, legacy applications
The people who benefit most from Sonatype Auditor are those who manage monolithic applications that have little to no current development being done on them. I repeat: little to no development being done. Sonatype Auditor works best when your legacy application is still integral to the organization and necessary to meet a variety of industry standards. The most popular standards that I run into are ISO and SOC2 compliance.
The other use case for Sonatype Auditor is to understand what open source components are utilized in outsourced, third-party application development. Sonatype Auditor notifies you if those applications pose a security or legal risk.
To be clear, you need software composition analysis. This way you know the third party, open source components within a legacy application. With a software bill of materials you know exactly what is inside an application. You need to analyze and understand the risk exposure of outdated open source components.
Everyone benefits from a software bill of materials (SBOM)
Sonatype Auditor enables your organization to automatically generate a software bill of materials to help identify open source components within your legacy and third-party applications. We also provide you with the ability to triage license and security risks.
What I like best about this functionality is the visualization. Sonatype Auditor helps you quickly see the severity of your risk. It also shows which version of the component is safe, and which is most utilized within the industry. This also provides you with the ability to continuously monitor applications for new risks and the ability to triage before being exposed to risk.
Need integrations? Sonatype Lifecycle or Sonatype Lifecycle Foundation are better solutions
If you are looking for integrations into your IDE of choice, such as Jenkins, or Jira, this indicates you're actively developing and upgrading applications. In that case, Sonatype Auditor is not the best solution for you.
If you are looking for integrations, Sonatype Lifecycle or Sonatype Lifecycle Foundation provide automated component scanning and more robust, ongoing security protection. They provide everything Sonatype Auditor does, plus more.
Today, 1 out of 10 components downloads will contain a known vulnerability. While your application is safe today, it may not be tomorrow, three months from now, or six months from now. So the question becomes, how do you manage open source risk in production or third-party applications? I invite you to contact me and learn more about your options and what will work best for you. Yes, the best solution for you could be Sonatype Auditor. But, in competitive environments actively producing new software, Sonatype Lifecycle is your friend.
As PSAs say, "the more you know."