Did you know there is a place at the U.S. Department of Defense (DoD) that is tasked with deploying technology capabilities in 0 to 2 years? For the DoD - or government in general - that is impressive. But, what if you knew that they are averaging 23 days for an accredited capability?
The DoD’s Joint Improvised Threat Defeat Organization (JIDO), J6, has that task, and their Chief Technology Officer talked about his organization’s transformational journey at one of our previous ADDO conferences. Leonel Garciga (Leo) shared how they get requirements deployed faster and more robust at scale and within a secure perspective: we thought it was worth revisiting.
For anyone that has worked in defense, you know everyone works to support the mission, whether they are on the front lines or processing contracts at the Pentagon. Leo knew it was critical that they get everyone on the same page from a mission perspective of they were going to deliver secure, accredited capabilities at an accelerated pace.
Besides being focused on the mission, everyone needs to know who their customer is - and that varies depending on their role. For development, the customer is the end-user, and they need to focus on the user, not goals within the development cycle. However, for operations and information assurance, the development team is their customer.
With the team focused on the mission and customers, they need the right tools. They invested in software delivery and make sure everyone uses the same tool for consistency and reliability. This mean that sometimes they need to connect legacy capabilities to leverage what they have. Along those lines, Leo advised:
“Adaptability is greater than correctness.”
While you might have to work with legacy systems, you can’t stop looking to innovation, and, in government, they have to look at industry and the national labs to see what they are doing and adopt it where it makes sense. They can’t become insular or arrogant.
Of course, this all sets the foundation for the work, but what guides the day-to-day? As you might guess: DevOps. Leo mentioned that anyone that knows him at work has heard him say:
“DevOps is awesome!”
He embraces it, and looks to its full potential. He mentioned that most government implementations fall short of true DevOps as their value chain stops at staging. But Leo knows that isn’t DevOps. To be DevOps, the value chain has to go all the way through to production.
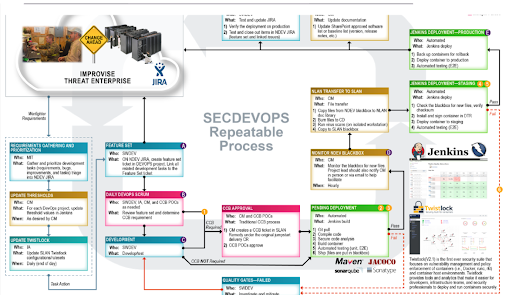
They also try and automate everything in the pipeline to reduce human error and provide an audit trail. Their goal is: no manual and human review gates. And, because DevOps allows for an auditable track to show what you are doing and how you got there, this is how they get true, ongoing authorizations.
During his talk, he presented the formula for maximum agility:
Secure Agile + DevOps + Continuous Monitoring = Ongoing Authorization.
Automation mitigates risk because it allows for the following to be enforced in the development process:
- Code supply chain management
- Container scanning for critical vulnerabilities
- Automated testing
- Test driven development and code-level unit test coverage
- Static code analysis
- Penetration testing
- Requirements management system
In the end, Leo presented why having a DevOps pipeline is a CIO/CISO’s imperative:
- Single pane of glass for capability delivery and risk assessment so you can have a better sense of the risk you are putting onto the network
- Baked in regulatory and auditing functions
- Real-time visibility into assessing risk and continuous monitoring
- Real-time visibility into project status and automated documentation
- Repeatable processes with metrics
- Standardized deployment and mitigation methodology
- Transparency out to the customer







