In two minutes, we can show you a full software bill of materials for your application. We can also identify any known vulnerabilities in the open source and third-party components within your Java application. Oh, and by the way, it’s free.
That’s right, at Sonatype, we could not be more in favor of the code reuse that occurs millions of times a day thanks to the availability of open source and third-party components. At the same time, we are steadfastly against the reuse of known vulnerable versions of components in your applications. Spread the good, not the bad. Simple, right?
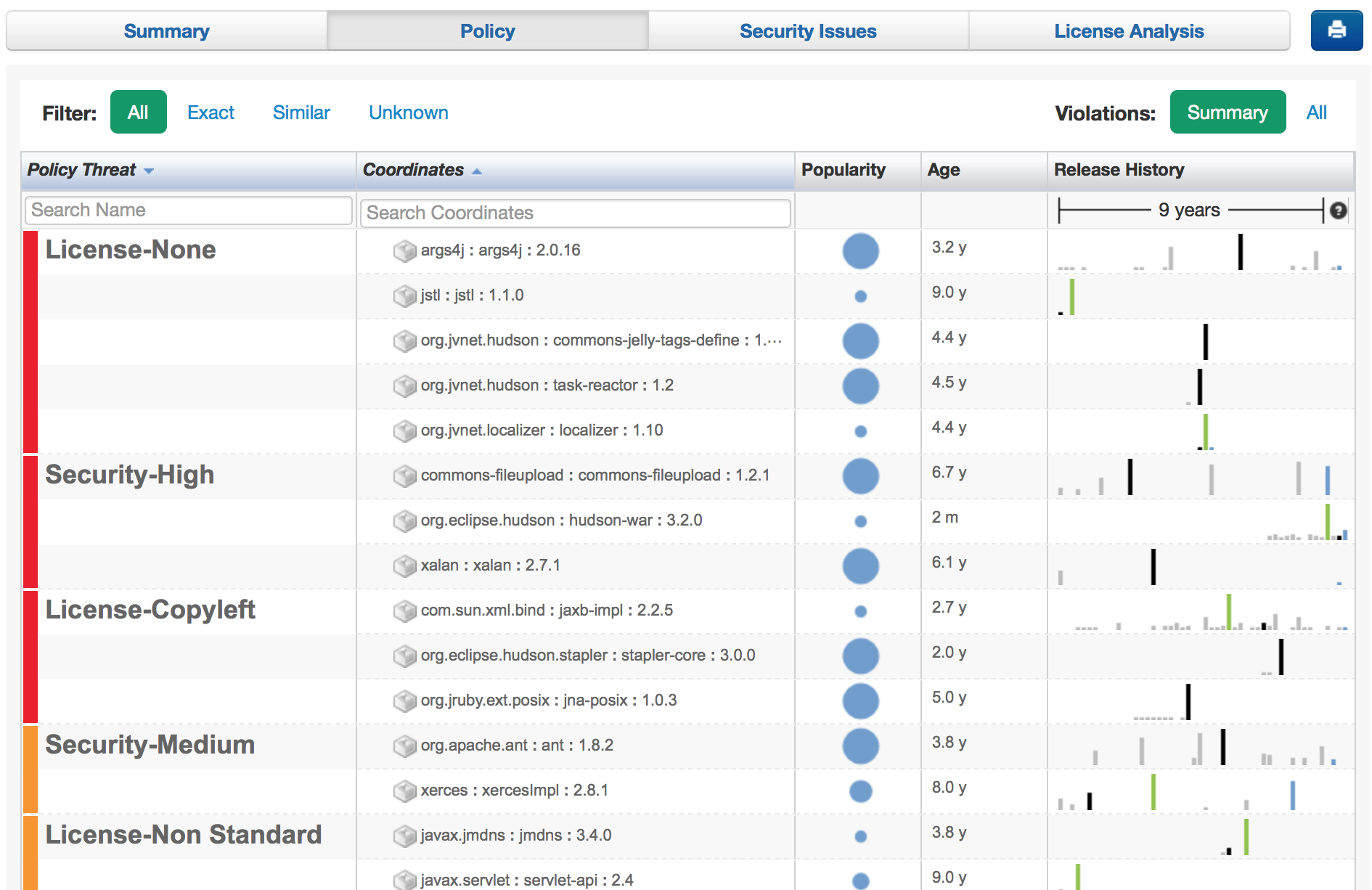
Where other worthwhile approaches to application security might take hours or even days to return actionable insight, our open source risk assessment can return a summary of known vulnerabilities and license risks in under two minutes. All you have to do is download our small analysis app. You will also have access to a full software Bill of Materials -- listing all open source and third-party components used in your app.
Oh, and one more thing: you do not upload your app to us for analysis -- it stays with you the whole time.
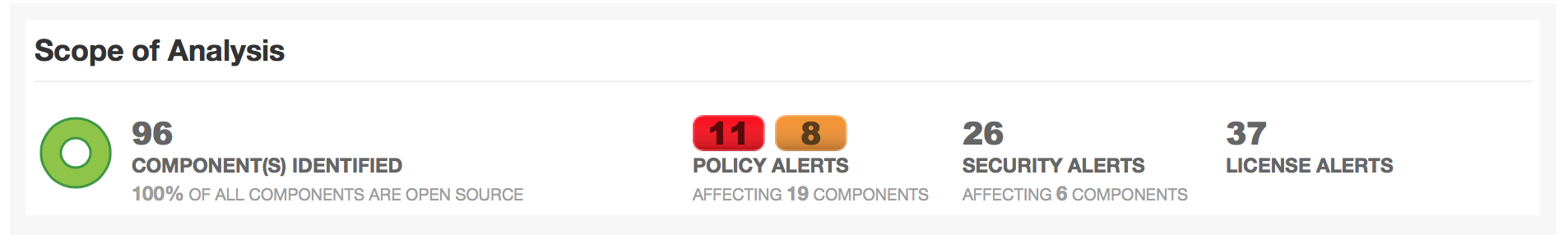
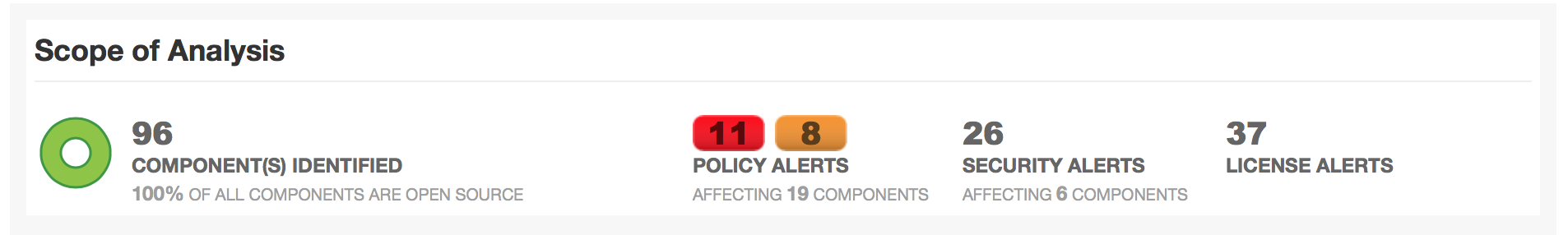
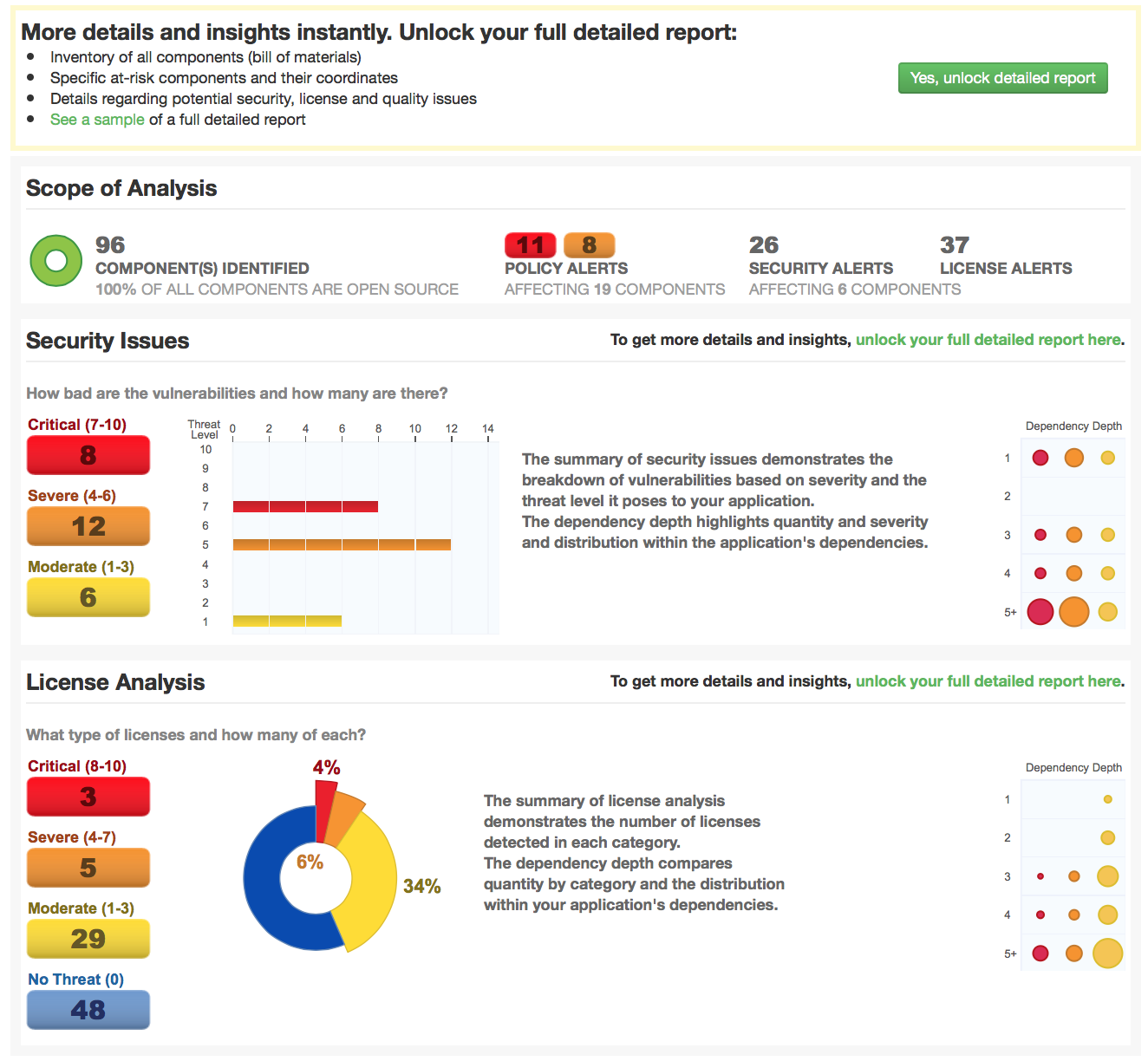
When 90% of typical modern application might be composed of open source components, a quick analysis is worth your while. What does the multi-page report look like? It starts with this executive summary of the software bill of materials. Check it out:
Want to analyze your known vulnerabilities and license risks within your own app? You can skip to Application Health Check right now.
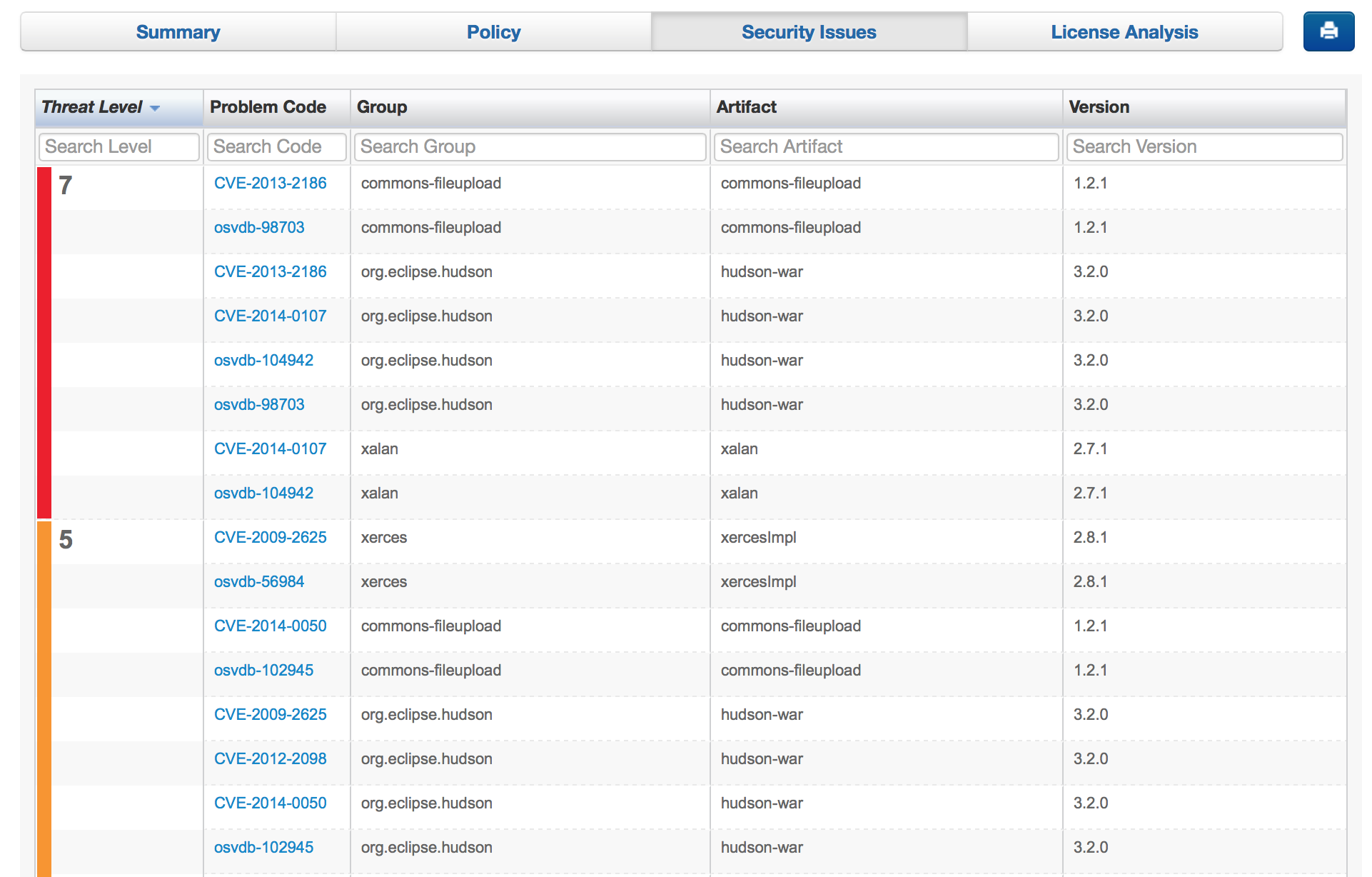
But, hey what about specifics? If your analysis summary does happen to return with known open source risks, we can send you all of the details for each component. The details will not only be delivered promptly, they will also be clear and actionable. Here are some sample of the security violation details (again, all free to you):
Within the same report, you will also receive a complete software Bill of Materials of the open source components used within your application. This is a great asset that can be used with your own application or for Java applications you might be using from other vendors.
Our new and improved Application Health Check is an open source risk assessment offered as a free community service. As part of our mission to help you build trusted applications and keep them that way over time, we hope this service can help your organization identify avoidable open source risks in the applications you build for your own clients and customers.
And finally, if you are free at 1pm ET tomorrow (October 22), join us for a conversation with Nigel Simpson, Director of Architecture for a very large media and entertainment company. Nigel will be sharing his experiences in building a policy to help his organization ban avoidable open source software risks, while avoiding unnecessary rework for thousands of developers worldwide. You can find the registration for this event here.