This week in malware we discovered and analyzed nearly 100 packages flagged as malicious, suspicious, or dependency confusion attacks.
Notably, we uncovered a PyPI package that drops fileless Linux malware directly in memory to covertly run a cryptominer. Furthermore, our investigation revealed the threat actor published this malicious package under the stolen identity of a software engineer from a United States National Laboratory.
secretslib PyPI package identified as fileless Linux malware
In this rundown of malware, Sonatype's automated detection system identified PyPI package secretslib as potentially malicious.
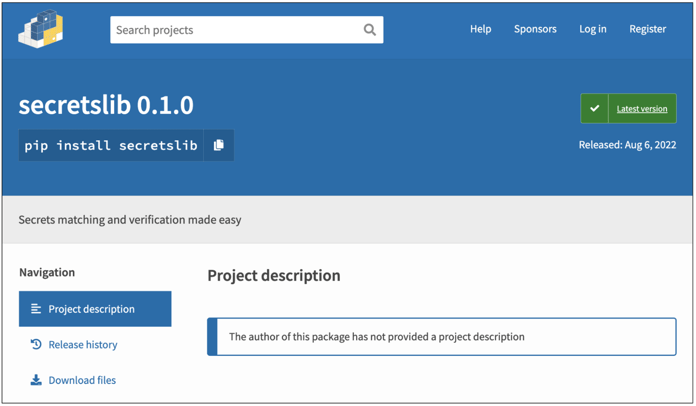
At its release, the package contained the description "secrets matching and verification made easy." Upon investigation, the package contained a different kind of secret — it runs cryptominers on your Linux machine in-memory, directly from your RAM. We see this technique to a great extent with fileless malware and crypters.
Additionally, the threat actor who published the malicious package impersonated a real software engineer who works for a science and engineering research laboratory funded by the U.S. Department of Energy.
For a deep dive on how secretslib used a quasi-clean stripped ELF binary to drop a Linux cryptominer in memory, read Ax Sharma's dedicated blog post.
More packages: Malicious, suspicious, dependency confusion
We caught the following this week via Sonatype's automated malware detection system, offered as a part of Sonatype Repository Firewall:
@luckygoats/xray3-lab
@mgmresorts/cart-components
@mgmresorts/wcl-lab
@quidditch/private_pkg_2
after-exec
aiogram-types
ci-cd-tools
clarity-atoms
codemirror-dart-minifier
com.apple.core
com.google.play.billing
conda-verifyyyyy
create-closure-releases
default-difficulties
docs-local-mocks
docusign.myclick
docusign.myclick.nondisclosureagreement
docusign.termsandconditions
donuts.node-weak
drgn-tokenization
dukaan-requests
evankin
express-okta-oath
express-uzeragent
federalist-admin
front-analytics
gaarf-fetch-cf
gatsby-pancake-api
gcore-cdn-stats
gen-mapping
ib-staking-rewards-test
iftta
iotex-explorer
kings-landing-obfuscate
ks/kw-logs
kwaishop-digital-access-demo
kwaishop-logs
kwaishop-sdk
kwaishop-utils
live-commerce
magic-internet-money
marketplace-benchmarks
martinez-api-test
meesho-pow
meesho_farmiso_customer_frontend
messenger-quick-start
mew-connect-handshake-server
mobstor
nequi-api-utils
ngx-infinite-scroll-fixed
nns-dapp
node-example.ts
pancake-info-api
pancake-lottery-scheduler
performance-quality-models-nodejs
presence-service
prevent-nosqli
preventxss
private_pkgs
prmetrics
ptokens-website-backend
python-drgn
react-server-dom-vite
react_popper_old
router-governance
rush-mock-flush-telemetry-plugin
scfg-foundation
secretslib
sensei-lms
staketool
subnet-evm-contracts
supplier-panel-v2
sxg-playground
test-loader-utils
test6a1i4los
testdonotinstall
tezos-sdk
token_supply
tokenary-web3-provider
tolerant-php-parser-server
tracking-pixel
triggerator-backend
ts_utils_for_sxg_rs
valyrian-debug
vscode-eslint
vscode-lsp
vscode-tsconfig-gen
vsts-tasks-jenkinsqueuejob
wireit-extension
xray-lab
xray2-lab
xray22-lab
zerion-analytics
zksync-zkwallet-vue
These discoveries follow our report last week of typosquats and ransomware scripts in PyPI.
Turn on Sonatype Repository Firewall for automatic protection
As a DevSecOps organization, we remain committed to identifying and halting attacks, such as those mentioned above, against open source developers and the wider software supply chain.
Users of Sonatype Repository Firewall can rest easy knowing that such malicious packages would automatically be blocked from reaching their development builds.

Sonatype Repository Firewall instances will automatically quarantine any suspicious components detected by our automated malware detection systems while a manual review by a researcher is in progress, thereby keeping your software supply chain protected from the start.
Sonatype's world-class security research data, combined with our automated malware detection technology safeguards your developers, customers, and software supply chain from infections.